Typeform, Popular Online Survey Software, Suffers Data Breach
Typeform, the popular Spanish-based online data collection company specializes in form building and online surveys for businesses worldwide, has today disclosed that the company has suffered a data breach that exposed partial data of its some users. The company identified the breach on June 27th,…
RAMpage Attack Explained—Exploiting RowHammer On Android Again!
A team of security researchers has discovered a new set of techniques that could allow hackers to bypass all kind of present mitigations put in place to prevent DMA-based Rowhammer attacks against Android devices. Dubbed RAMpage, the new technique (CVE-2018-9442) could re-enable an unprivileged Android…
Ticketmaster Suffers Security Breach – Personal and Payment Data Stolen
Global entertainment ticketing service Ticketmaster has admitted that the company has suffered a security breach, warning customers that their personal and payment information may have been accessed by an unknown third-party. The company has blamed a third-party support customer service chat application for the data…
New Malware Family Uses Custom UDP Protocol for C&C Communications
Security researchers have uncovered a new highly-targeted cyber espionage campaign, which is believed to be associated with a hacking group behind KHRAT backdoor Trojan and has been targeting organizations in South East Asia. According to researchers from Palo Alto, the hacking group, which they dubbed…
Default Passwords Aid Satori IoT Botnet Attacks
Researchers at Netlab 360 detected a surge in malicious activity scanning and infecting several IoT devices, attempting to make them part of Satori, a variant of the Mirai IoT botnet that is used to take down websites and mine digital coins. Experts point to lack of oversight…
Google Home’s data leak proves the IoT is still deeply flawed
Google / WIRED / Artizarus The Internet of Things (IoT) security problem isn’t going away. The connected network of billions of devices – from smart doorbells to office printers – is regularly found to have privacy problems and be open to attack by potential hackers….
Magento Hackers Using Simple Evasion Trick to Reinfect Sites With Malware
Security researchers have been warning of a new trick that cybercriminals are leveraging to hide their malicious code designed to re-introduce the infection to steal confidential information from Magento based online e-commerce websites. So, if you have already cleaned up your hacked Magento website, there…
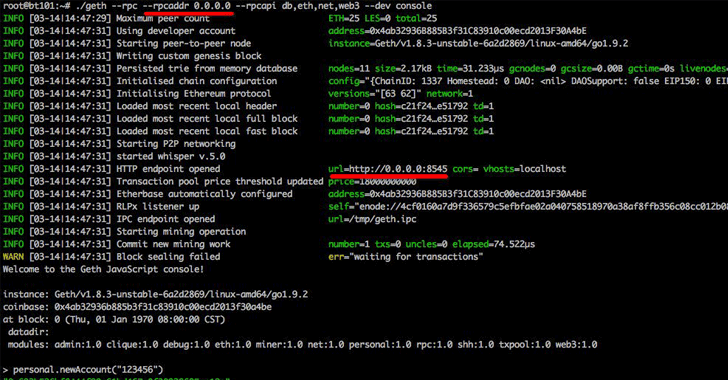
Hackers Stole Over $20 Million in Ethereum from Insecurely Configured Clients
Researchers have been warning about cyber attacks wherein attackers made over 20 million dollars by hijacking insecurely configured Ethereum nodes exposed on the Internet. Qihoo 360 Netlab in March tweeted about a group of cybercriminals who were scanning the Internet for port 8545 to find insecure geth…
Amazon Fire TV and Fire TV Stick Miner Infections on the Rise
Following the large number of viruses that are being developed for Android and iOS devices, latest news is that a large number of Amazon Fire TV and Fire TV Stick devices are being targeted by cryptocurrency miners. The hackers have developed numerous forms of malicious…
How Mirai spawned the current IoT malware landscape
When, in late 2016, US-based DNS provider Dyn suffered a massive DDoS attack that it resulted in the temporary unavailability of many popular online services, the name of the Mirai malware became instantly known outside the cybersecurity industry. Since then, we’ve come to know the…







Stay connected