According to Avira, hundreds of thousands of unpatched Windows systems are serially infected with EternalBlue exploit code.
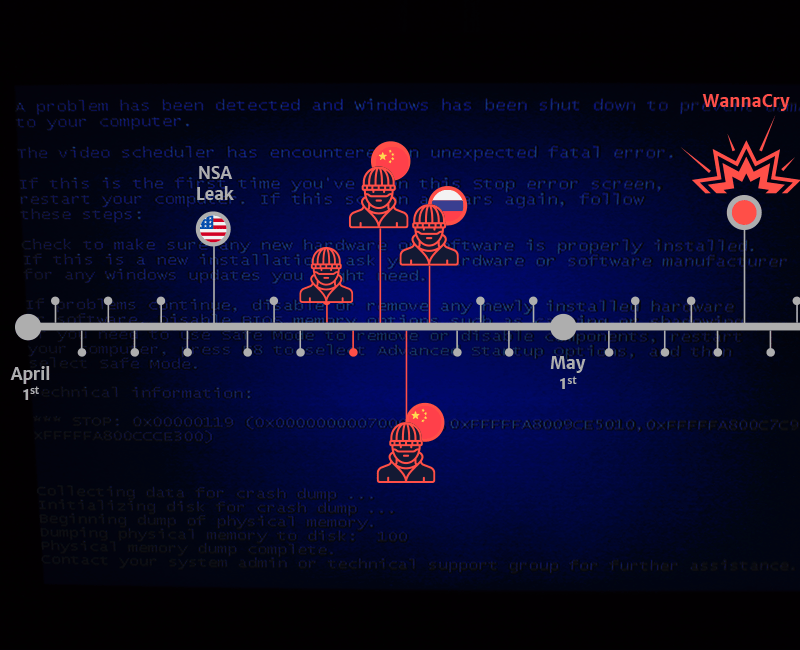
The EternalBlue, is the alleged NSA exploit that made the headlines with DOUBLEPULSAR in the WannaCry attack.
The malicious code was leaked online by the Shadow Brokers hacking group that stole it from the arsenal of the NSA-linked Equation Group.
ETERNALBLUE targets the Server Message Block SMBv1 protocol on port 445, it has become widely adopted in the community of malware developers to target Windows 7 and Windows XP systems.
Microsoft addressed the flaw with the MS17-010 and also released an emergency patch for Windows XP and Server 2003 in response to the WannaCry ransomware attacks.
According to a new blog post published by Avira, unpatched systems remain exposed to cyber attacks and are serially infected by threat actors.
“There are still significant numbers of repeatedly infected machines more than a year after the big WannaCry and Petya attacks,” said Mikel Echevarria-Lizarraga, senior virus analyst in the Avira Protection Lab.
“Our research has linked this to Windows machines that haven’t been updated against the NSA Eternal Blue exploit and are an open target for malware.”
The number of unpatched systems exposed online is very high, experts pointed out that most of them have been infected multiple times, they were found to run cracked Windows installations this means that they did not receive Microsoft’s security updates.
“We were researching the reasons behind a number of machines having repeated infections,” added Mikel. “We’ve found that many of these serially infected machines were running activation cracks which means that they cannot or do not want to update Windows and install updates. It also means that they did not receive the March 2018 emergency patch from Microsoft for this vulnerability.”
Avira decided to turn off the SMB1 protocol entirely on the infected machine to stop the endless infection loop.
The experts discovered around 300,000 computers affected by the issue and the Avira Protection whatever is deactivating the SMB1 protocol on around 14,000 computers daily.
The list of the top ten countries for serially infected machines is:
- Indonesia
- Taiwan
- Vietnam
- Thailand
- Egypt
- Russia
- China
- Philippines
- India
- Turkey
The above list doesn’t surprise the experts, according to studies from Statista, the above countries are top nations for the use of unlicensed software.
“The predominance of infected machines outside of North America and Europe roughly parallels studies from Statista on the use of unlicensed software.” concluded AVIRA.
“This study found unlicensed software rates averaging around 52 – 60% outside the United States and the European Union and fell to 16% and 28% respectively in these areas. Unlicensed software is usually unable to get the latest patches against vulnerabilities such as EternalBlue.”
Source:
https://securityaffairs.co/wordpress/76313/hacking/windows-eternalblue-exploit.html