1. EXECUTIVE SUMMARY
- CVSS v3 2.4
- ATTENTION: Low skill level to exploit
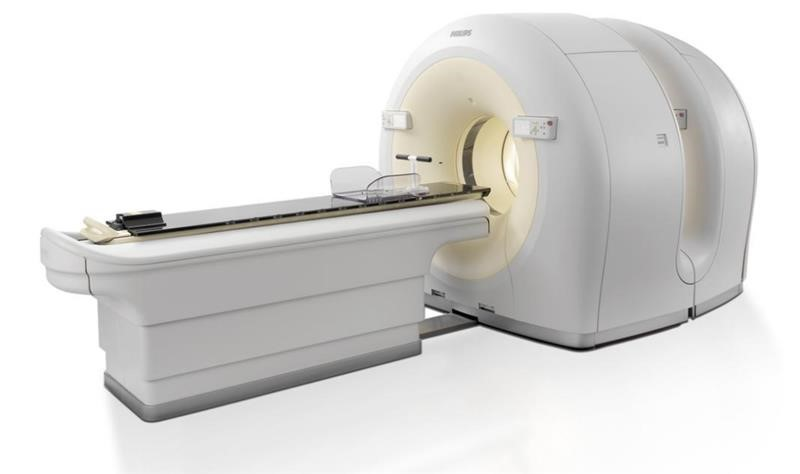
- Vendor: Philips
- Equipment: Gemini PET/CT Family
- Vulnerability: Storage of Sensitive Data in a Mechanism Without Access Control
2. RISK EVALUATION
Successful exploitation of this vulnerability involving removable media could allow access to sensitive information (including patient information).
3. TECHNICAL DETAILS
3.1 AFFECTED PRODUCTS
Philips reports the vulnerability affects the following Gemini PET/CT products:
- 882300 Gemini 16 Slice
- 882160 Gemini Dual
- 882400 Gemini GXL 10 Slice
- 882390 Gemini GXL 6 Slice
- 882410 Gemini GXL 16 Slice
- 882412 GEMINI LXL
- 882473 Gemini TF Ready
- 882470 Gemini TF 16 w/ TOF Performance
- 882471 Gemini TF 64 w/ TOF Performance
- 882476 Gemini TF Big Bore
- 882438 TruFlight Select PET/CT
3.2 VULNERABILITY OVERVIEW
3.2.1 STORAGE OF SENSITIVE DATA IN A MECHANISM WITHOUT ACCESS CONTROL CWE-921
The software stores sensitive information in a removable media device that does not have built-in access control.
CVE-2021-27456 has been assigned to this vulnerability. A CVSS v3 base score of 2.4 has been calculated; the CVSS vector string is (AV:P/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N).
3.3 BACKGROUND
- CRITICAL INFRASTRUCTURE SECTORS: Healthcare and Public Health
- COUNTRIES/AREAS DEPLOYED: Worldwide
- COMPANY HEADQUARTERS LOCATION: Netherlands
3.4 RESEARCHER
Jean GEORGE – CHU UCL Namur – Nuclear medicine department reported this vulnerability to Philips.
4. MITIGATIONS
Philips has identified the following guidance and mitigations:
- Users should operate all Philips deployed and supported Gemini PET/CT systems within Philips authorized specifications, including Philips approved software, software configuration, system services, and security configuration.
- Philips also recommends users implement a comprehensive, multi-layered strategy to protect systems from internal and external security threats, including restricting physical access of the scanner and removable media to only authorized personnel to reduce the risk of physical access by an unauthorized user.
- Patient health related information recorded on removable media may become accessible to unauthorized individuals despite the application of the anonymize function, which could create a security risk.
Users with questions regarding their specific installations of the Gemini PET/CT Family should contact a Philips service support team. Philips contact information is available at https://www.usa.philips.com/healthcare/solutions/customer-service-solutions or 1-800-722-9377
The Philips advisory is available. Please see the Philips product security website for the latest security information for Philips products.
CISA recommends users take defensive measures to minimize the risk of exploitation of this vulnerability. CISA reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures.
CISA also provides a section for control systems security recommended practices on the ICS webpage on us-cert.cisa.gov. Several recommended practices are available for reading and download, including Improving Industrial Control Systems Cybersecurity with Defense-in-Depth Strategies.
Additional mitigation guidance and recommended practices are publicly available on the ICS webpage on us-cert.cisa.gov in the Technical Information Paper, ICS-TIP-12-146-01B–Targeted Cyber Intrusion Detection and Mitigation Strategies.
Organizations observing any suspected malicious activity should follow their established internal procedures and report their findings to CISA for tracking and correlation against other incidents.
No known public exploits specifically target this vulnerability. This vulnerability is not exploitable remotely.
Source: