1. EXECUTIVE SUMMARY
- CVSS v3 9.8
- ATTENTION: Exploitable remotely/low attack complexity
- Vendor: Schneider Electric
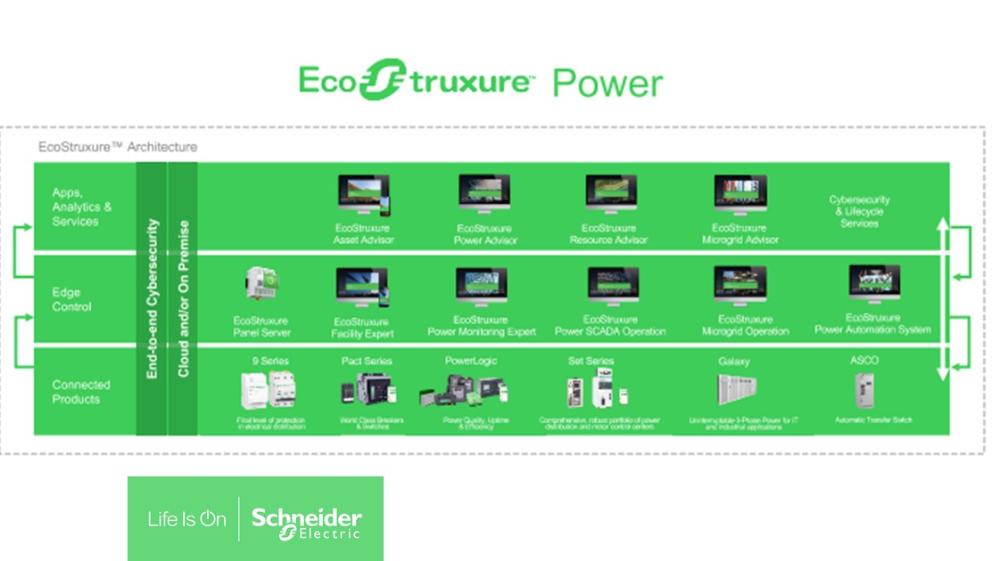
- Equipment: EcoStruxure Power Monitoring Expert, EcoStruxure Power Operation with Advanced Reports, EcoStruxure Power SCADA
Operation with Advanced Reports - Vulnerability: Deserialization of Untrusted Data
2. RISK EVALUATION
Successful exploitation of this vulnerability could allow an attacker to achieve remote code execution.
3. TECHNICAL DETAILS
3.1 AFFECTED PRODUCTS
The following version of Schneider Electric EcoStruxure Power Monitoring Expert and Power Operation Products is affected:
- EcoStruxure Power Monitoring Expert: All versions prior to Hotfix-145271
- EcoStruxure Power Operation with Advanced Reports: All versions prior to application of Hotfix-145271
- EcoStruxure Power SCADA Operation with Advanced Reports: All versions prior to Hotfix-145271
3.2 Vulnerability Overview
3.2.1 DESERIALIZATION OF UNTRUSTED DATA CWE-502
A deserialization of untrusted data vulnerability exists that could allow an attacker to execute arbitrary code on the targeted system by sending a specifically crafted packet to the application.
CVE-2023-5391 has been assigned to this vulnerability. A CVSS v3 base score of 9.8 has been calculated; the CVSS vector string is (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H).
3.3 BACKGROUND
- CRITICAL INFRASTRUCTURE SECTORS: Multiple
- COUNTRIES/AREAS DEPLOYED: Worldwide
- COMPANY HEADQUARTERS LOCATION: France
4. MITIGATIONS
Schneider Electric has released the following mitigations/fixes for the following products:
- EcoStruxure Power Monitoring Expert: A Hotfix for this vulnerability is available by contacting Contact Schneider Electric’s Customer Care Center. The Hotfix can be applied to versions PME 2023, 2022, and 2021, the versions currently in support on the date of this disclosure. Previous versions, please contact customer care to inquire about upgrade paths.
- EcoStruxure Power Operation with Advanced Reports and EcoStruxure Power SCADA Operation with Advanced Reports: A Hotfix for this vulnerability is available by contacting Contact Schneider Electric’s Customer Care Center. The Hotfix can be applied to versions EPO 2022, and 2021, the versions currently in support on the date of this disclosure. Previous versions, please contact customer care to inquire about upgrade paths.
Schneider Electric also recommends the following cybersecurity best practices:
- Locate control and safety system networks and remote devices behind firewalls and isolate them from the business network.
- Install physical controls so no unauthorized personnel can access your industrial control and safety systems, components, peripheral equipment, and networks.
- Place all controllers in locked cabinets and never leave them in the “Program” mode.
- Never connect programming software to any network other than the network intended for that device.
- Scan all methods of mobile data exchange with the isolated network such as CDs, USB drives, etc. before use in the terminals or any node connected to these networks.
- Never allow mobile devices that have connected to any other network besides the intended network to connect to the safety or control networks without proper sanitation.
- Minimize network exposure for all control system devices and systems and ensure that they are not accessible from the Internet.
- When remote access is required, use secure methods, such as virtual private networks (VPNs). Recognize that VPNs may have vulnerabilities and should be updated to the most current version available. Also, understand that VPNs are only as secure as the connected devices.
For more information refer to the Schneider Electric Recommended Cybersecurity Best Practices document.
For further information, see Schnieder Electric’s Security Advisory.
CISA reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures.
CISA also provides a section for control systems security recommended practices on the ICS webpage on cisa.gov/ics. Several CISA products detailing cyber defense best practices are available for reading and download, including Improving Industrial Control Systems Cybersecurity with Defense-in-Depth Strategies.
CISA encourages organizations to implement recommended cybersecurity strategies for proactive defense of ICS assets.
Additional mitigation guidance and recommended practices are publicly available on the ICS webpage at cisa.gov/ics in the technical information paper, ICS-TIP-12-146-01B–Targeted Cyber Intrusion Detection and Mitigation Strategies.
Organizations observing suspected malicious activity should follow established internal procedures and report findings to CISA for tracking and correlation against other incidents.
No known public exploitation specifically targeting this vulnerability has been reported to CISA at this time.
5. UPDATE HISTORY
- October 17, 2023: Initial Publication
This product is provided subject to this Notification and this Privacy & Use policy.
Vendor
Schneider Electric
Source: