. EXECUTIVE SUMMARY
-
CVSS v3 5.3
- ATTENTION: Exploitable remotely/low skill level to exploit
- Vendor: Siemens
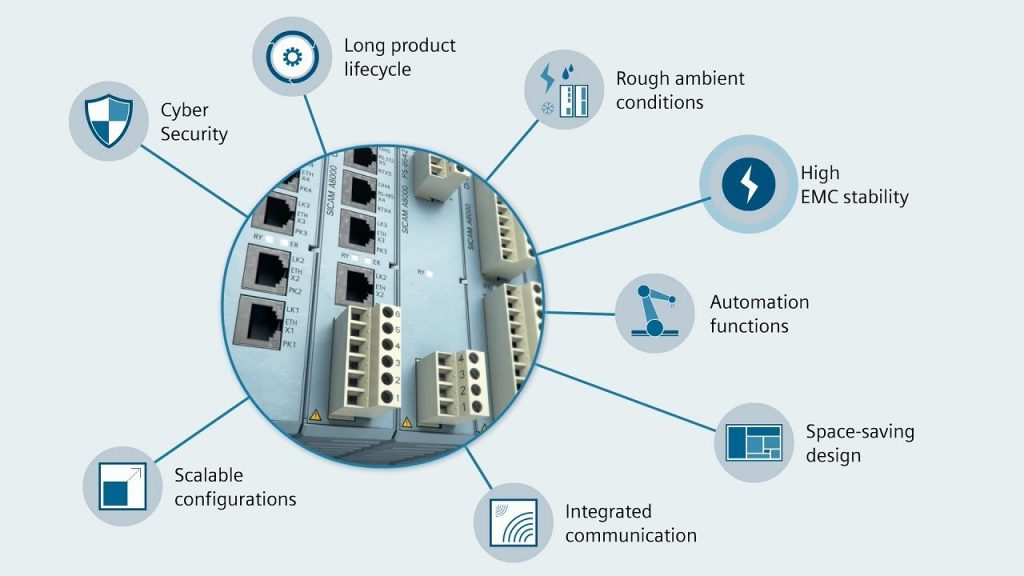
- Equipment: SICAM A8000 RTU
- Vulnerability: Uncaught Exception
2. RISK EVALUATION
The SICAM A8000 RTU series is affected by a security vulnerability that could allow unauthenticated remote users to cause a denial-of-service condition on the web server of affected products.
3. TECHNICAL DETAILS
3.1 AFFECTED PRODUCTS
The following versions of SICAM A8000 RTU, a telecontrol and automation device, are affected:
- SICAM A8000 CP-8000 versions prior to v14,
- SICAM A8000 CP-802X versions prior to v14, and
- SICAM A8000 CP-8050 versions prior to v2
3.2 VULNERABILITY OVERVIEW
3.2.1 UNCAUGHT EXCEPTION CWE-248
Specially crafted network packets sent to Ports 80/TCP or 443/TCP could allow an unauthenticated remote attacker to cause a denial-of-service condition on a web server.
CVE-2018-13798 has been assigned to this vulnerability. A CVSS v3 base score of 5.3 has been assigned; the CVSS vector string is (AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:L).
3.3 BACKGROUND
- CRITICAL INFRASTRUCTURE SECTORS: Energy
- COUNTRIES/AREAS DEPLOYED: Worldwide
- COMPANY HEADQUARTERS LOCATION: Germany
3.4 RESEARCHER
Emanuel Duss and Nicolas Heiniger from Compass Security reported this vulnerability to Siemens.
4. MITIGATIONS
Siemens has released updates for all product variants and recommends users update to the new versions:
https://support.industry.siemens.com/cs/search?search=a8000%20cp8000
Siemens has identified the following specific workarounds and mitigations users can apply to reduce the risk:
- Limit access to the web server on Ports 80/TCP and 443/TCP with an external firewall.
- Apply a Defense-in-Depth strategy.
NCCIC recommends users take defensive measures to minimize the risk of exploitation of this vulnerability. Specifically, users should:
- Minimize network exposure for all control system devices and/or systems, and ensure that they are not accessible from the Internet.
- Locate control system networks and remote devices behind firewalls, and isolate them from the business network.
- When remote access is required, use secure methods, such as Virtual Private Networks (VPNs), recognizing that VPNs may have vulnerabilities and should be updated to the most current version available. Also recognize that VPN is only as secure as the connected devices.
NCCIC reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures.
NCCIC also provides a section for control systems security recommended practices on the ICS-CERT web page. Several recommended practices are available for reading and download, including Improving Industrial Control Systems Cybersecurity with Defense-in-Depth Strategies.
Additional mitigation guidance and recommended practices are publicly available on the ICS-CERT website in the Technical Information Paper, ICS-TIP-12-146-01B–Targeted Cyber Intrusion Detection and Mitigation Strategies.
Organizations observing any suspected malicious activity should follow their established internal procedures and report their findings to NCCIC for tracking and correlation against other incidents.
No known public exploits specifically target this vulnerability.
Source:
https://ics-cert.us-cert.gov/advisories/ICSA-19-038-01