1. EXECUTIVE SUMMARY
- CVSS v3 8.8
- ATTENTION: Exploitable remotely/low skill level to exploit
- Vendor: Siemens
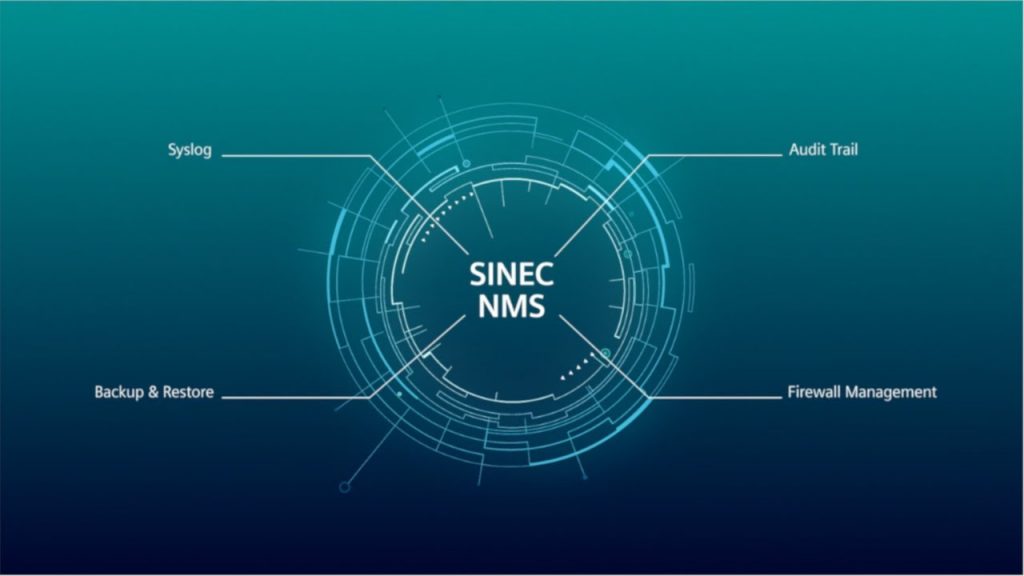
- Equipment: SINEMA Server, SINEC NMS
- Vulnerability: Path Traversal
2. RISK EVALUATION
Successful exploitation of this vulnerability could allow arbitrary code execution on an affected system.
3. TECHNICAL DETAILS
3.1 AFFECTED PRODUCTS
The following versions of Siemens products, are affected:
- SINEC NMS: All versions prior to v1.0 SP1 Update 1
- SINEMA Server: All versions prior to v14.0 SP2 Update 2
3.2 VULNERABILITY OVERVIEW
3.2.1 IMPROPER LIMITATION OF A PATHNAME TO A RESTRICTED DIRECTORY (‘PATH TRAVERSAL’) CWE-22
When uploading files to an affected system using a zip container, the system does not correctly check if the relative file path of the extracted files is still within the intended target directory. An attacker could exploit this vulnerability to create or overwrite arbitrary files on an affected system.
CVE-2020-25237 has been assigned to this vulnerability. A CVSS v3 base score of 8.8 has been calculated; the CVSS vector string is (AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H).
3.3 BACKGROUND
- CRITICAL INFRASTRUCTURE SECTORS: Chemical, Energy, Food and Agriculture, Water and Wastewater Systems
- COUNTRIES/AREAS DEPLOYED: Worldwide
- COMPANY HEADQUARTERS LOCATION: Germany
3.4 RESEARCHER
rgod, working with Trend Micro’s Zero Day Initiative, reported this vulnerability to CISA.
4. MITIGATIONS
Siemens has published security advisory SSA-156833 that further describes how this vulnerability affects SINEC NMS and SINEMA Server. Siemens recommends users update their products to the latest version.
Siemens has identified the following specific workarounds and mitigations users can apply to reduce risk:
- Restrict access to the affected components to trusted personnel.
As a general security measure, Siemens strongly recommends users protect network access to devices with appropriate mechanisms. In order to operate the devices in a protected IT environment, Siemens recommends users configure the environment according to Siemens’ operational guidelines for industrial security, and follow the recommendations in the product manual.
Additional information on industrial security by Siemens can be found at: https://www.siemens.com/industrialsecurity
CISA recommends users take defensive measures to minimize the risk of exploitation of this vulnerability. Specifically, users should:
- Minimize network exposure for all control system devices and/or systems, and ensure that they are not accessible from the Internet.
- Locate control system networks and remote devices behind firewalls, and isolate them from the business network.
- When remote access is required, use secure methods, such as Virtual Private Networks (VPNs), recognizing that VPNs may have vulnerabilities and should be updated to the most current version available. Also recognize that VPN is only as secure as the connected devices.
CISA reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures.
CISA also provides a section for control systems security recommended practices on the ICS webpage on us-cert.cisa.gov. Several recommended practices are available for reading and download, including Improving Industrial Control Systems Cybersecurity with Defense-in-Depth Strategies.
Additional mitigation guidance and recommended practices are publicly available on the ICS webpage on us-cert.cisa.gov in the Technical Information Paper, ICS-TIP-12-146-01B–Targeted Cyber Intrusion Detection and Mitigation Strategies.
Organizations observing any suspected malicious activity should follow their established internal procedures and report their findings to CISA for tracking and correlation against other incidents.
No known public exploits specifically target this vulnerability.
Source: