1. EXECUTIVE SUMMARY
- CVSS v3 9.1
- ATTENTION: Exploitable remotely/low attack complexity
- Vendor: ThroughTek
- Equipment: P2P SDK
- Vulnerability: Cleartext Transmission of Sensitive Information
2. RISK EVALUATION
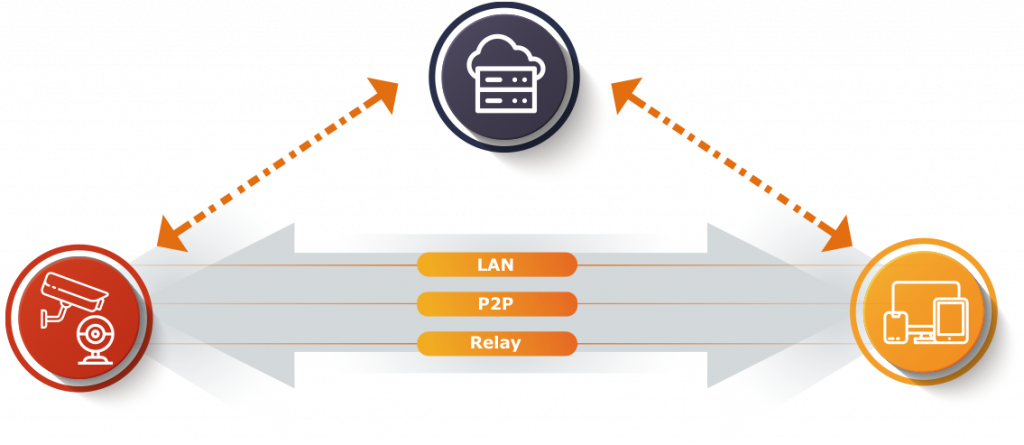
ThroughTek supplies multiple original equipment manufacturers of IP cameras with P2P connections as part of its cloud platform. Successful exploitation of this vulnerability could permit unauthorized access to sensitive information, such as camera audio/video feeds.
3. TECHNICAL DETAILS
3.1 AFFECTED PRODUCTS
The following versions of P2P Software Development Kit (SDK) are affected:
- Versions 3.1.5 and prior
- SDK versions with nossl tag
- Device firmware that does not use AuthKey for IOTC connection
- Device firmware using the AVAPI module without enabling DTLS mechanism
- Device firmware using P2PTunnel or RDT module
3.2 VULNERABILITY OVERVIEW
3.2.1 CLEARTEXT TRANSMISSION OF SENSITIVE INFORMATION CWE-319
The affected ThroughTek P2P products do not sufficiently protect data transferred between the local device and ThroughTek servers. This can allow an attacker to access sensitive information, such as camera feeds.
CVE-2021-32934 has been assigned to this vulnerability. A CVSS v3 base score of 9.1 has been calculated; the CVSS vector string is (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:N).
3.3 BACKGROUND
- CRITICAL INFRASTRUCTURE SECTORS: Communications
- COUNTRIES/AREAS DEPLOYED: Worldwide
- COMPANY HEADQUARTERS LOCATION: Taiwan
3.4 RESEARCHER
Nozomi Networks reported this vulnerability to CISA.
4. MITIGATIONS
ThroughTek recommends original equipment manufacturers to implement the following mitigations:
- If SDK is Version 3.1.10 and above, enable authkey and DTLS.
- If SDK is any version prior to 3.1.10, upgrade library to v3.3.1.0 or v3.4.2.0 and enable authkey/DTLS.
Additional information can be found in ThroughTek’s advisory.
CISA recommends users take defensive measures to minimize the risk of exploitation of this vulnerability. Specifically, users should:
- Minimize network exposure for all control system devices and/or systems, and ensure that they are not accessible from the Internet.
- Locate control system networks and remote devices behind firewalls, and isolate them from the business network.
- When remote access is required, use secure methods, such as Virtual Private Networks (VPNs), recognizing VPNs may have vulnerabilities and should be updated to the most current version available. Also recognize VPN is only as secure as its connected devices.
CISA reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures.
CISA also provides a section for control systems security recommended practices on the ICS webpage on us-cert.cisa.gov. Several recommended practices are available for reading and download, including Improving Industrial Control Systems Cybersecurity with Defense-in-Depth Strategies.
Additional mitigation guidance and recommended practices are publicly available on the ICS webpage on us-cert.cisa.gov in the Technical Information Paper, ICS-TIP-12-146-01B–Targeted Cyber Intrusion Detection and Mitigation Strategies.
Organizations observing any suspected malicious activity should follow their established internal procedures and report their findings to CISA for tracking and correlation against other incidents.
No known public exploits specifically target this vulnerability.
Source: