1. EXECUTIVE SUMMARY
-
CVSS v3 6.8
- ATTENTION: Low skill level to exploit
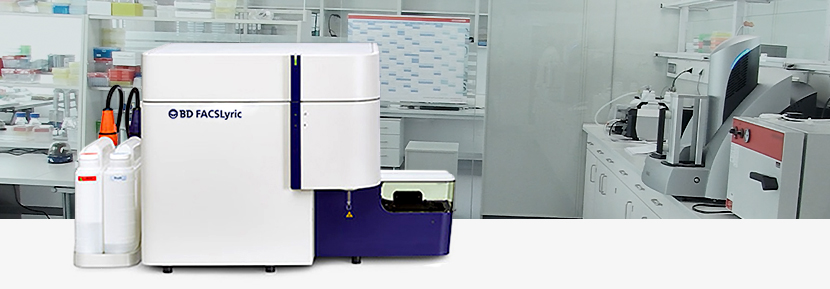
- Vendor: Becton, Dickinson and Company (BD)
- Equipment: FACSLyric
- Vulnerability: Improper Access Control
2. RISK EVALUATION
Successful exploitation of this vulnerability may allow an attacker to gain unauthorized access to administrative level privileges on a workstation, which could allow arbitrary execution of commands. This vulnerability does not impact BD FACSLyric flow cytometry systems using the Windows 7 Operating System.
3. TECHNICAL DETAILS
3.1 AFFECTED PRODUCTS
The following versions of the FACSLyric flow cytometry solution are affected:
- BD FACSLyric Research Use Only, Windows 10 Professional Operating System, U.S. and Malaysian Releases, between November 2017 and November 2018, and
- BD FACSLyric IVD Windows 10 Professional Operating System U.S. release.
3.2 VULNERABILITY OVERVIEW
3.2.1 IMPROPER ACCESS CONTROL CWE-284
The application does not properly enforce user access control to privileged accounts, which may allow for unauthorized access to administrative level functions.
CVE-2019-6517 has been assigned to this vulnerability. A CVSS v3 base score of 6.8 has been calculated; the CVSS vector string is (AV:P/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H).
3.3 BACKGROUND
- CRITICAL INFRASTRUCTURE SECTORS: Healthcare and Public Health
- COUNTRIES/AREAS DEPLOYED: Worldwide
- COMPANY HEADQUARTERS LOCATION: United States
3.4 RESEARCHER
BD reported this vulnerability to NCCIC.
4. MITIGATIONS
BD will follow-up directly with all affected users to perform remediation activities. BD will disable the administrative account for users with BD FACSLyric RUO Cell Analyzer units having the Windows 10 Pro Operating System. BD has contacted and will replace the computer workstations for affected users with the BD FACSLyric IVD Cell Analyzer units with the Windows 10 Pro Operating System.
For additional information regarding the reported vulnerability please contact BD for the following support:
For technical support, please contact the BD Biosciences General Tech Support – Flow Cytometry via email researchapplications@bd.com or phone 877-232-8995 Option 2 and then Option 2 again.
For more information on BD’s product security and vulnerability management, contact BD’s Product Security Office:
https://www.bd.com/productsecurity
NCCIC recommends users take defensive measures to minimize the risk of exploitation of this vulnerability. Specifically, users should:
- Minimize network exposure for all medical devices and/or systems.
- Locate medical devices behind firewalls, and isolate them where possible.
- Restrict system access to authorized personnel only and follow a least privilege approach.
- Apply defense-in-depth strategies.
- Disable unnecessary accounts and services.
NCCIC reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures.
NCCIC also provides a section for control systems security recommended practices on the ICS-CERT web page. Several recommended practices are available for reading and download, including Improving Industrial Control Systems Cybersecurity with Defense-in-Depth Strategies.
Additional mitigation guidance and recommended practices are publicly available on the ICS-CERT website in the Technical Information Paper, ICS-TIP-12-146-01B–Targeted Cyber Intrusion Detection and Mitigation Strategies.
Organizations observing any suspected malicious activity should follow their established internal procedures and report their findings to NCCIC for tracking and correlation against other incidents.
No known public exploits specifically target this vulnerability. This vulnerability is not exploitable remotely.
Source:
https://ics-cert.us-cert.gov/advisories/ICSMA-19-029-02