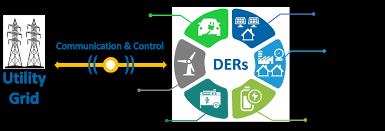
Distributed Energy Resources Cybersecurity Outlook:Vulnerabilities, Attacks, Impacts, and Mitigations
Abstract—The digitization and decentralization of the electric power grid are key thrusts for an economically and environmentally sustainable future. Towards this goal, distributed energy resources (DER), including rooftop solar panels, battery storage, electric vehicles, etc., are becoming ubiquitous in power systems. Power utilities benefit from…
POWER OUT?
SOLARINVERTERS AND THESILENT CYBER THREAT What’s the problem? As Australia accelerates adoption of renewable energy sources, new cyber securityvulnerabilities are being introduced through Internet of Things (IoT) devices. Cyber securityconcerns about these devices, notably photovoltaic inverters (solar inverters), have recentlycome to the fore, and policy…
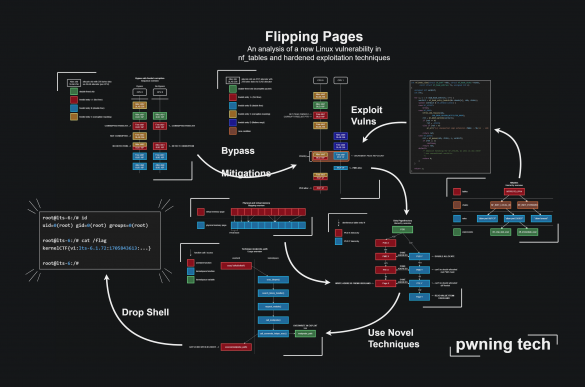
Flipping Pages: An analysis of a new Linux vulnerability in nf_tables and hardened exploitation techniques-Part II
4. Techniques 4.1. Page refcount juggling The first technique required for the exploit is juggling page refcounts. When we attempt to double-free a page in the kernel using the dedicated API functions, the kernel will check the refcount of the page: Codeblock 4.1.1: C code…
Flipping Pages: An analysis of a new Linux vulnerability in nf_tables and hardened exploitation techniques
This blogpost is the next instalment of my series of hands-on no-boilerplate vulnerability research blogposts, intended for time-travellers in the future who want to do Linux kernel vulnerability research. Specifically, I hope beginners will learn from my VR workflow and the seasoned researchers will learn…
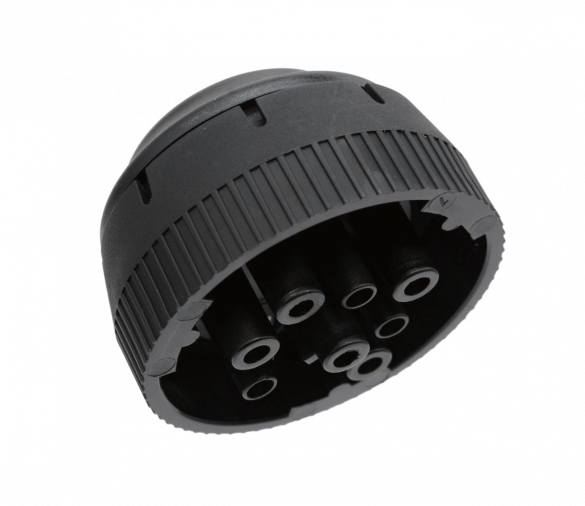
IOSIX IO-1020 Micro ELD
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an adjacent attacker to take control of vehicle systems by connecting to and modifying the affected device. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following IOSiX products are affected: 3.2 Vulnerability Overview…
Cisco Access Point Software Secure Boot Bypass Vulnerability
Summary A vulnerability in the boot process of Cisco Access Point (AP) Software could allow an unauthenticated, physical attacker to bypass the Cisco Secure Boot functionality and load a software image that has been tampered with on an affected device. This vulnerability exists because unnecessary…
Cisco IOS XR Software for ASR 9000 Series Aggregation Services Routers PPPoE Denial of Service Vulnerability
Summary A vulnerability in the PPP over Ethernet (PPPoE) termination feature of Cisco IOS XR Software for Cisco ASR 9000 Series Aggregation Services Routers could allow an unauthenticated, adjacent attacker to crash the ppp_ma process, resulting in a denial of service (DoS) condition. This vulnerability…
GhostRace: Exploiting and Mitigating Speculative Race Conditions
Race conditions arise when multiple threads attempt to ac- cess a shared resource without proper synchronization, often leading to vulnerabilities such as concurrent use-after-free. To mitigate their occurrence, operating systems rely on syn- chronization primitives such as mutexes, spinlocks, etc. In this paper, we present…
Critical Vulnerability Allows Access to QNAP NAS Devices
Taiwan-based QNAP Systems over the weekend announced patches for multiple vulnerabilities impacting its products, including a critical-severity bug leading to unauthenticated device access. Tracked as CVE-2024-21899 (CVSS score of 9.8), the vulnerability is described as an improper authentication issue that “could allow users to compromise…
Cisco Secure Client Carriage Return Line Feed Injection Vulnerability
Summary A vulnerability in the SAML authentication process of Cisco Secure Client could allow an unauthenticated, remote attacker to conduct a carriage return line feed (CRLF) injection attack against a user. This vulnerability is due to insufficient validation of user-supplied input. An attacker could exploit…






Stay connected