Oracle Releases Security Updates
Oracle has released its Critical Patch Update Advisory, Solaris Third Party Bulletin, and Linux Bulletin for July 2023 to address vulnerabilities affecting multiple products. A remote attacker can exploit some of these vulnerabilities to take control of an affected system. Oracle Linux Bulletin – July 2023…
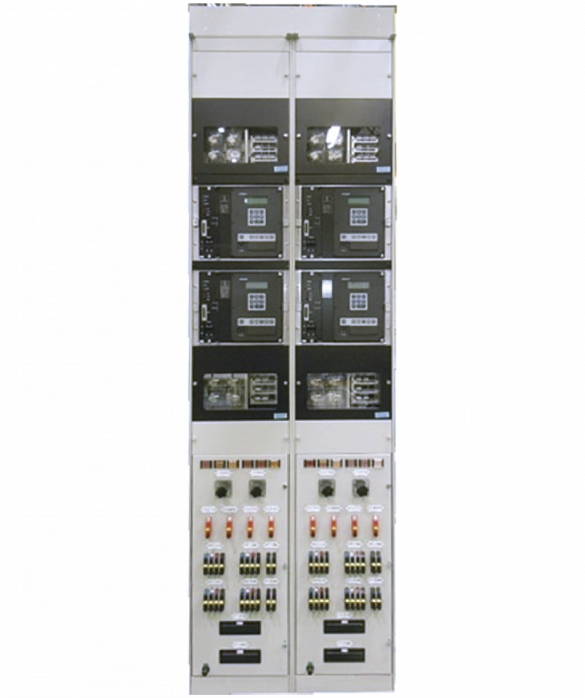
Nokia ASIK AirScale System Module
1. EXECUTIVE SUMMARY CVSS v3 8.4 ATTENTION: Low attack complexity Vendor: Nokia Equipment: ASIK AirScale 5G Common System Module Vulnerabilities: Improper Access Control for Volatile Memory Containing Boot Code, Assumed-Immutable Data is Stored in Writable Memory 2. RISK EVALUATION Successful exploitation of these vulnerabilities could result in the execution…
VMware Releases Security Updates
VMware has released security updates to address multiple vulnerabilities in VMware Cloud Foundation. A remote attacker could exploit one of these vulnerabilities to take control of an affected system. Multiple vulnerabilities were privately reported to VMware. Updates are available to address this vulnerability in affected…
Siemens Siveillance Video Mobile Server
1. EXECUTIVE SUMMARY CVSS v3 9.4 ATTENTION: Exploitable remotely/low attack complexity Vendor: Siemens Equipment: Siveillance Video 2022 R2 Vulnerability: Weak Authentication 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an unauthenticated remote attacker to access the application without a valid account. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS…
CISCO Identity Services Engine Unauthorized File Access Vulnerability
A vulnerability in the web-based management interface of Cisco Identity Services Engine (ISE) could allow an authenticated, remote attacker to read and delete files on an affected device.This vulnerability is due to insufficient validation of user-supplied input. An attacker could exploit this vulnerability by sending…
Hitachi Energy APM Edge (Update A)
1. EXECUTIVE SUMMARY CVSS v3 8.2 ATTENTION: Low attack complexity Vendor: Hitachi Energy Equipment: Transformer Asset Performance Management (APM) Edge Vulnerability: Reliance on Uncontrolled Component 2. UPDATE OR REPOSTED INFORMATION This updated advisory is a follow-up to the original advisory titled “ICSA-21-336-06 Hitachi Energy APM Edge” that was published…
CISA Releases RedEye: Red Team Campaign Visualization and Reporting Tool
CISA has released RedEye, an interactive open-source analytic tool to visualize and report Red Team command and control activities. RedEye allows an operator to quickly assess complex data, evaluate mitigation strategies, and enable effective decision making. RedEye is an open-source analytic tool developed by CISA…
Measuresoft ScadaPro Server
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low attack complexity Vendor: Measuresoft Equipment: ScadaPro Server Vulnerability: Improper Access Control 2. RISK EVALUATION Successful exploitation of this vulnerability could allow a local user with limited privileges to modify the service binary path and start malicious commands with SYSTEM privileges. 3….
Delta Industrial Automation DIAEnergie
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/Low attack complexity Vendor: Delta Industrial Automation Equipment: DIAEnergie Vulnerability: Use of Hard-coded Credentials 2. RISK EVALUATION Successful exploitation of this vulnerability could lead to remote code execution. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Delta Industrial Automation reports the following versions…
AVEVA Edge 2020 R2 SP1 and all prior versions
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low attack complexity Vendor: AVEVA Equipment: AVEVA Edge 2020 R2 SP1 and all prior versions Vulnerabilities: Insufficient UI Warning of Dangerous Operations, Uncontrolled Search Path Element, Deserialization of Untrusted Data, Improper Restriction of XML External Entity Reference 2. RISK EVALUATION Successful exploitation…









Stay connected