VMware Releases Security Advisory for Aria Operations
Security Advisory: VMSA-2024-0001 1. Impacted Products 2. Introduction A Missing Access Control vulnerability in Aria Automation has been privately reported to VMware. Updates are available to remediate this vulnerability in affected VMware products. 3. Aria Automation Missing Access Control Vulnerability (CVE-2023-34063) Description: Aria Automation contains…
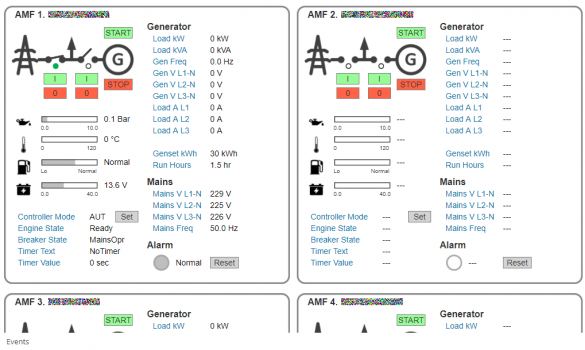
Multiple Vulnerabilities in Rapid SCADA Pose Serious Threats, Urgent Mitigations Recommended
Executive Summary: Rapid Software LLC’s industrial automation platform, Rapid SCADA, has been found susceptible to multiple critical vulnerabilities, posing significant risks of remote code execution, unauthorized access, and privilege escalation. The Cybersecurity and Infrastructure Security Agency (CISA) issued an advisory detailing the potential exploits and…
Mitsubishi Electric MELSEC iQ-R, Q and L Series
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could cause a denial-of-service condition in the Ethernet port on the CPU module. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Mitsubishi Electric reports that the following MELSEC programmable controllers are affected: 3.2 Vulnerability Overview 3.2.1 Uncontrolled…
Johnson Controls Metasys and Facility Explorer
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to cause a denial-of-service by sending invalid credentials. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of Johnson Controls Metasys and Facility Explorer are affected: 3.2 Vulnerability Overview 3.2.1 UNCONTROLLED…
Siemens SINEC INS
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to create a denial-of-service condition, intercept credentials, or escalate privileges on the affected device. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following Siemens products are affected: 3.2 Vulnerability Overview 3.2.1 IMPROPER…
Zebra ZTC Industrial ZT400 and ZTC Desktop GK420d
Executive SummaryCVSS v3 5.4ALERT: Vulnerable to exploitation with adjacent access/low attack complexityManufacturer: Zebra TechnologiesDevices: ZTC Industrial ZT410, ZTC Desktop GK420dIssue: Potential Authentication Bypass via Alternate Path or Channel Risk AssessmentSuccessful exploitation of this vulnerability could permit an unauthorized individual to manipulate credentials by sending specifically…
Siemens SIMATIC PCS neo
SIMATIC PCS neo: Versions before V4.13.2 Vulnerability Overview3.2.1 MISSING AUTHENTICATION FOR CRITICAL FUNCTION CWE-306Affected products’ PUD Manager fails to authenticate users properly within its web service. This allows an unauthenticated attacker from an adjacent network to generate a privileged token and upload additional documents.CVE-2023-46096 has…
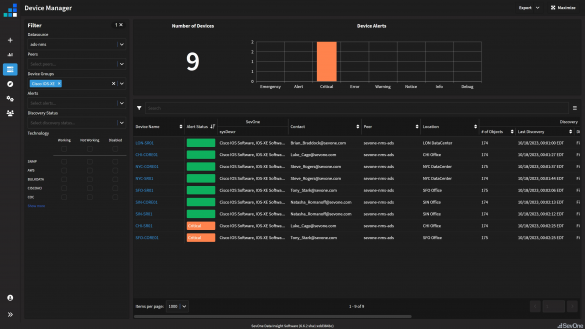
Cisco IOS XE Software Web UI Feature
Summary Affected Products Details Indicators of Compromise Workarounds Fixed Software Recommendations
CISA Releases Guidance for Addressing Cisco IOS XE Web UI Vulnerabilities
SummaryCisco has provided an update regarding the ongoing investigation into the observed exploitation of the web UI feature in Cisco IOS XE Software. The initial fixed software releases are now available on the Cisco Software Download Center. Cisco will continue to update the advisory as…
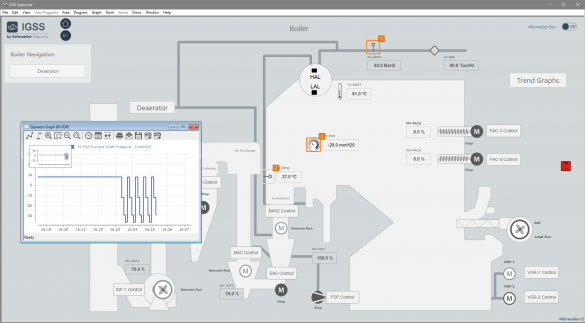
Schneider Electric IGSS
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow arbitrary code execution or loss of control of the SCADA system. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Schneider Electric reports these vulnerabilities affect the following IGSS (Interactive Graphical SCADA System) products: 3.2…








Stay connected