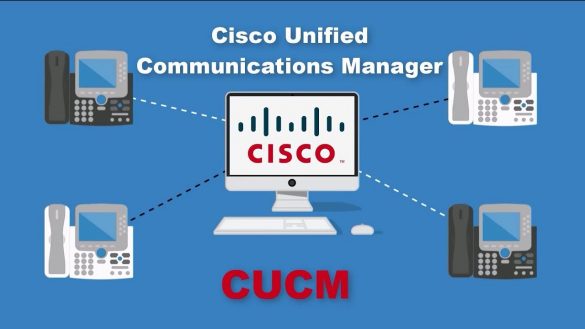
Cisco Unified Communications Products Remote Code Execution Vulnerability
Summary Affected Products Products Confirmed Not Vulnerable Only products listed in the Vulnerable Products section of this advisory are known to be affected by this vulnerability. Cisco has confirmed that this vulnerability does not affect the following Cisco products: Workarounds Additionally, follow the best practices that are…
Passive SSH Key Compromise via Lattices
ABSTRACTWe demonstrate that a passive network attacker can opportunistically obtain private RSA host keys from an SSH server that experiences a naturally arising fault during signature computation. In prior work, this was not believed to be possible for the SSH protocol because the signature included…
Terrapin Attack: Breaking SSH Channel IntegrityBy Sequence Number Manipulation
Abstract The SSH protocol provides secure access to network services, particularly remote terminal login and file transfer within organizational networks and to over 15 million servers on the open internet. SSH uses an authenticated key exchange to establish a secure channel between a client and…
Siemens SCALANCE and RUGGEDCOM M-800/S615 Family
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker with administrative privileges to execute arbitrary code on the affected device. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following products of Siemens, are affected: 3.2 Vulnerability Overview 3.2.1 ACCEPTANCE OF EXTRANEOUS…
Windows API Exploitation in Real World By Akash Sarode
Cyber Security in today’s world has become more challenging thantraditional days where we had Firewall and antivirus as our main defensesystems. Modern day adversary have got all the necessary resources – (Time,Team & Money) to execute their tasks of getting a victim compromised. Mostof the…
BLUFFS: Bluetooth Forward and Future Secrecy Attacks andDefenses
ABSTRACTBluetooth is a pervasive technology for wireless communication.Billions of devices use it in sensitive applications and to exchangeprivate data. The security of Bluetooth depends on the Bluetoothstandard and its two security mechanisms: pairing and session establishment. No prior work, including the standard itself, analyzed the…
Everlasting ROBOT: the Marvin Attack
Abstract. In this paper we show that Bleichenbacher-style attacks onRSA decryption are not only still possible, but also that vulnerable implementations are common. We have successfully attacked multiple implementations using only timing of decryption operation and shown thatmany others are vulnerable. To perform the attack…
Ubuntu Security Notice USN-6502-1
Packages Details Ivan D Barrera, Christopher Bednarz, Mustafa Ismail, and Shiraz Saleemdiscovered that the InfiniBand RDMA driver in the Linux kernel did notproperly check for zero-length STAG or MR registration. A remote attackercould possibly use this to execute arbitrary code. (CVE-2023-25775) Yu Hao discovered that…
Mitsubishi Electric MELSEC and MELIPC Series (Update G)
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow a remote attacker to cause a denial-of-service condition. Recovery requires a system reset. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of MELSEC series CPU modules and MELIPC Series Industrial Computers…
Hitachi Energy eSOMS
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to disclose sensitive information related to eSOMS application configuration. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following Hitachi Energy products are affected: 3.2 Vulnerability Overview 3.2.1 GENERATION OF ERROR MESSAGE CONTAINING…








Stay connected