Siemens Automation License Manager
1. EXECUTIVE SUMMARY CVSS v3 7.3 ATTENTION: Low skill level to exploit Vendor: Siemens Equipment: Automation License Manager (ALM) Vulnerability: Improper Authorization 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to locally escalate privileges and modify files that should be protected against writing. 3. TECHNICAL…
Siemens SICAM A8000 RTUs
1. EXECUTIVE SUMMARY CVSS v3 8.3 ATTENTION: Exploitable remotely Vendor: Siemens Equipment: SICAM A8000 Vulnerability: Cross-site Scripting 2. RISK EVALUATION Successful exploitation of this vulnerability could compromise the confidentiality, integrity, and availability of the web application. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of SICAM A8000 RTUs…
Siemens Opcenter Execution Core (Update A)
1. EXECUTIVE SUMMARY CVSS v3 8.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Opcenter Execution Core Vulnerabilities: Cross-site Scripting, SQL Injection, Improper Access Control 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-20-196-07 Siemens Opcenter Execution Core that was published…
Siemens UMC Stack
1. EXECUTIVE SUMMARY CVSS v3 6.7 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: UMC Stack Vulnerabilities: Unquoted Search Path or Element, Uncontrolled Resource Consumption, Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-20-196-05 Siemens UMC Stack that…
Siemens SIMATIC, SINAMICS, SINEC, SINEMA, SINUMERIK (Update B)
1. EXECUTIVE SUMMARY CVSS v3 6.7 ATTENTION: Low skill level to exploit Vendor: Siemens Equipment: SIMATIC, SINAMICS, SINEC, SINEMA, SINUMERIK Vulnerability: Unquoted Search Path or Element 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-20-161-04 Siemens SIMATIC, SINAMICS, SINEC, SINEMA, SINUMERIK (Update A)…
Siemens Industrial Products SNMP Vulnerabilities (Update B)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Various SCALANCE, SIMATIC, SIPLUS products Vulnerabilities: Data Processing Errors, NULL Pointer Dereference 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-20-042-02 Siemens Industrial Products SNMP Vulnerabilities (Update…
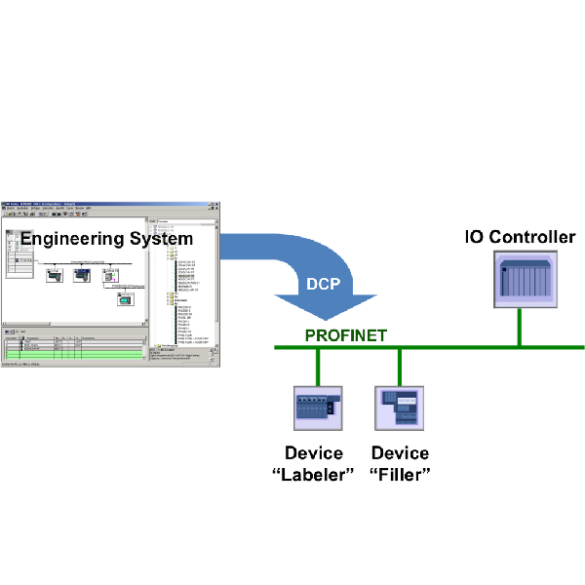
Siemens PROFINET-IO Stack (Update B)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Siemens PROFINET-IO Stack Vulnerability: Uncontrolled Resource Consumption 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-20-042-04 Siemens PROFINET-IO Stack (Update A) that was published March 10, 2020,…
Siemens Industrial Real-Time (IRT) Devices (Update D)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Industrial Real-Time (IRT) Devices Vulnerability: Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-19-283-01 Siemens Industrial Real-Time (IRT) Devices (Update C) that was published…
Siemens PROFINET Devices (Update G)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: PROFINET Devices Vulnerability: Uncontrolled Resource Consumption 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-19-283-02 Siemens PROFINET Devices (Update F) that was published July 14, 2020, to…
Siemens SIMATIC, SIMOCODE, SINAMICS, SITOP, and TIM
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC, SIMOCODE, SINAMICS, SITOP, and TIM Vulnerability: Out-of-bounds Read 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory titled ICSA-19-099-06 Siemens SIMATIC, SIMOCODE, SINAMICS, SITOP, and TIM (Update H)…









Stay connected