GE Proficy GDS
1. EXECUTIVE SUMMARY CVSS v3 8.2 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: General Electric (GE) Equipment: Proficy GDS Vulnerability: XXE 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to initiate an OPC UA session and retrieve an arbitrary file. 3. TECHNICAL DETAILS 3.1…
Philips HealthSuite Health Android App
1. EXECUTIVE SUMMARY CVSS v3 3.5 ATTENTION: Low skill level to exploit Vendor: Philips Equipment: Philips HealthSuite Health Android App Vulnerability: Inadequate Encryption Strength 2. RISK EVALUATION Successful exploitation of this vulnerability may allow an attacker with physical access to impact confidentiality and integrity of the product. 3. TECHNICAL…
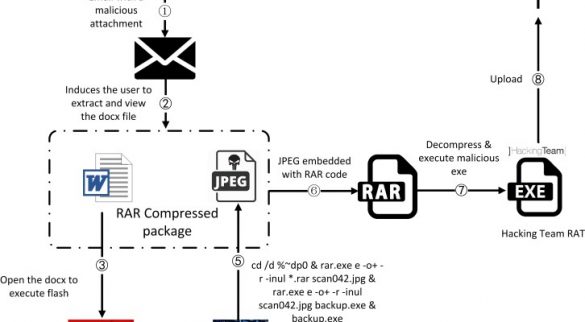
CVE-2018-15982 Adobe zero-day exploited in targeted attacks
Adobe released security updates for Flash Player that address two vulnerabilities, including a critical flaw, tracked as CVE-2018-15982, exploited in targeted attacks. Adobe fixed two flaws including a critical use-after-free bug, tracked as CVE-2018-15982, exploited by an advanced persistent threat actor aimed at a healthcare organization associated with…
Email accounts of top NRCC officials were hacked in 2018
Threat actors had access to the email accounts of at least four NRCC aides and spied on thousands of sent and received emails for several months. The email system at the National Republican Congressional Committee (NRCC), the Republican Party’s campaigning arm, was hacked. The news…
SamSam Ransomware
Summary The Department of Homeland Security (DHS) National Cybersecurity and Communications Integration Center (NCCIC) and the Federal Bureau of Investigation (FBI) are issuing this activity alert to inform computer network defenders about SamSam ransomware, also known as MSIL/Samas.A. Specifically, this product shares analysis of vulnerabilities…
SpiderControl SCADA WebServer
. EXECUTIVE SUMMARY CVSS v3 6.1 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: SpiderControl Equipment: SCADA WebServer Vulnerability: Reflected Cross-site Scripting 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to execute JavaScript on the victim’s browser. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following…
Omron CX-One
. EXECUTIVE SUMMARY CVSS v3 6.6 ATTENTION: Low skill level to exploit Vendor: Omron Equipment: CX-One Vulnerabilities: Stack-based Buffer Overflow, Use After Free 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to execute code under the privileges of the application. 3. TECHNICAL DETAILS 3.1 AFFECTED…
INVT Electric VT-Designer
1. EXECUTIVE SUMMARY CVSS v3 6.3 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: INVT Electric Equipment: VT-Designer Vulnerabilities: Deserialization of Untrusted Data, Heap-based Buffer Overflow 2. RISK EVALUATION Successful exploitation of these vulnerabilities could cause the program to crash and may allow remote code execution. 3. TECHNICAL DETAILS…
AVEVA Vijeo Citect and Citect SCADA
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low skill level to exploit Vendor: AVEVA Software, LLC (AVEVA) Equipment: Vijeo Citect, Citect SCADA Vulnerability: Uncontrolled Search Path Element 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to execute arbitrary code on the target system. 3. TECHNICAL…
3ve – Major Online Ad Fraud Operation
Systems Affected Microsoft Windows Overview This joint Technical Alert (TA) is the result of analytic efforts between the Department of Homeland Security (DHS) and the Federal Bureau of Investigation (FBI). DHS and FBI are releasing this TA to provide information about a major online ad fraud operation—referred…








Stay connected