Ovarro TBox
1. EXECUTIVE SUMMARY CVSS v3 8.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Ovarro Equipment: TBoxLT2 (All models), TBox MS-CPU32, TBox MS-CPU32-S2, TBox RM2 (All models), TBox TG2 (All models) Vulnerabilities: Code Injection, Incorrect Permission Assignment for Critical Resource, Uncontrolled Resource Consumption, Insufficiently Protected Credentials, Use of Hard-coded…
Rockwell Automation MicroLogix 1400 (Update A)
1. EXECUTIVE SUMMARY CVSS v3 8.1 ATTENTION: Exploitable remotely Vendor: Rockwell Automation Equipment: MicroLogix 1400 Vulnerability: Buffer Overflow 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-21-033-01 Rockwell Automation MicroLogix 1400 that was published February 2, 2021, to the…
Johnson Controls Exacq Technologies exacqVision
1. EXECUTIVE SUMMARY CVSS v3 5.3 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Exacq Technologies, Inc., a subsidiary of Johnson Controls Equipment: exacqVision Vulnerability: Information Exposure 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an unauthenticated attacker to view system-level information about the exacqVision Web Service…
Hitachi ABB Power Grids eSOMS Telerik
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Hitachi ABB Power Grids Equipment: eSOMS Telerik Vulnerabilities: Path Traversal, Deserialization of Untrusted Data, Improper Input Validation, Inadequate Encryption Strength, Insufficiently Protected Credentials, Path Traversal 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow…
Advantech WebAccess/SCADA
1. EXECUTIVE SUMMARY CVSS v3 5.4 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Advantech Equipment: WebAccess/SCADA Vulnerability: Cross-site Scripting 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an unauthorized user to steal a user’s cookie/session token or redirect an authorized user to a malicious webpage. 3….
Hitachi ABB Power Grids AFS Series
1. EXECUTIVE SUMMARY Hitachi ABB Power Grids AFS Series CVSS v3 6.5 ATTENTION: Low skill level to exploit Vendor: Hitachi ABB Power Grids Equipment: AFS Series Vulnerability: Infinite Loop 2. RISK EVALUATION Successful exploitation of this vulnerability could cause a denial-of-service condition on one of the ports in a…
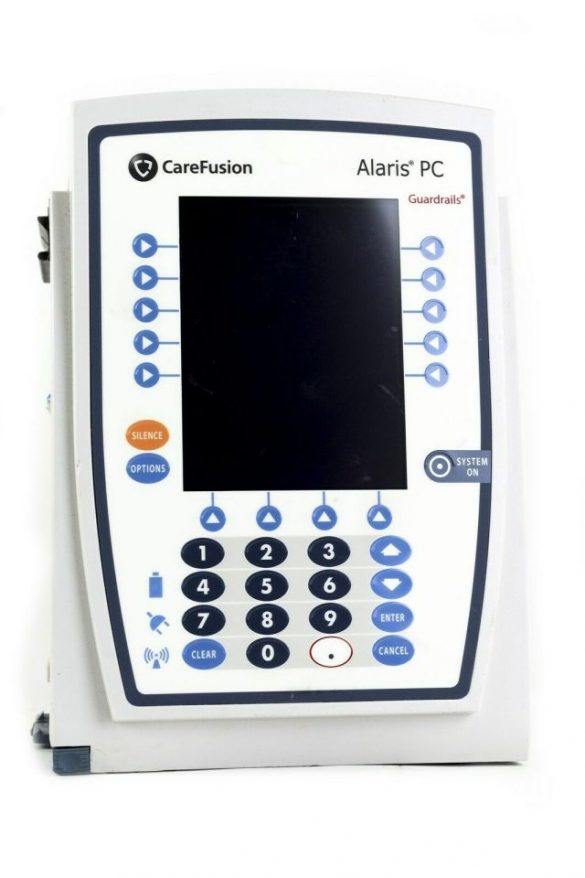
BD Alaris 8015 PC Unit (Update B)
1. EXECUTIVE SUMMARY CVSS v3 6.8 ATTENTION: Low skill level to exploit Vendor: Becton, Dickinson and Company (BD) Equipment: BD Alaris 8015 PC Unit Vulnerabilities: Insufficiently Protected Credentials, Security Features 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSMA-17-017-02 BD Alaris 8015 Insufficiently…
Schneider Electric IGSS SCADA Software
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low skill level to exploit Vendor: Schneider Electric Equipment: IGSS (Interactive Graphical SCADA System) Vulnerabilities: Improper Restriction of Operations within the Bounds of a Memory Buffer 2. RISK EVALUATION Successful exploitation of these vulnerabilities could result in remote code execution. 3. TECHNICAL…
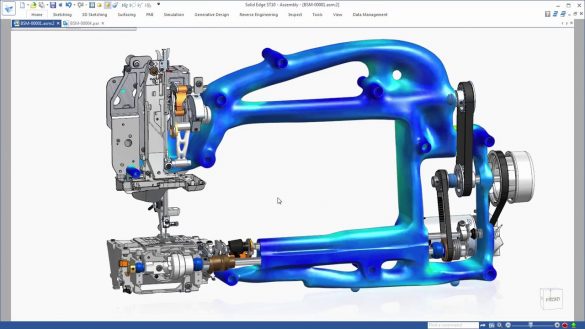
Siemens Solid Edge File Parsing
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low skill level to exploit Vendor: Siemens Equipment: Solid Edge Vulnerabilities: Out-of-bounds Write, Improper Restriction of XML External Entity Reference, Out-of-bounds Read 2. RISK EVALUATION Successful exploitation of these vulnerabilities could lead to a denial-of-service condition, and could lead to arbitrary code…
Luxion KeyShot (Update A)
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low skill level to exploit Vendor: Luxion Equipment: KeyShot products Vulnerabilities: Out-of-bounds Write, Out-of-bounds Read, Insufficient UI Warning of Dangerous Operations, Untrusted Pointer Dereference, Path Traversal 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-21-035-01 Luxion…








Stay connected