Siemens Industrial Real-Time (IRT) Devices
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Industrial Real-Time (IRT) Devices Vulnerability: Improper Input Validation 2. RISK EVALUATION Successful exploitation of this vulnerability could cause a denial-of-service condition. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Siemens reports the vulnerability affects the…
Siemens PROFINET Devices
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: PROFINET Devices Vulnerability: Uncontrolled Resource Consumption 2. RISK EVALUATION Successful exploitation of this vulnerability could cause a denial-of-service condition. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Siemens reports the vulnerability affects the following PROFINET…
Interpeak IPnet TCP/IP Stack (Update A)
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit/public exploits are available Vendors: ENEA, Green Hills Software, ITRON, IP Infusion, Wind River Equipment: OSE by ENEA, INTEGRITY RTOS by Green Hills Software, ITRON, ZebOS by IP Infusion, and VxWorks by Wind River Vulnerabilities: Stack-based Buffer…
Siemens SIMATIC WinCC and PCS7 (Update C)
. EXECUTIVE SUMMARY CVSS v3 7.2 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC WinCC and SIMATIC PCS7 Vulnerability: Unrestricted Upload of File with Dangerous Type 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-19-192-02 Siemens SIMATIC WinCC and PCS7…
Siemens SIMATIC PCS7, WinCC, TIA Portal (Update D)
1. EXECUTIVE SUMMARY CVSS v3 9.1 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC PCS7, WinCC Runtime Professional, WinCC (TIA Portal) Vulnerabilities: SQL Injection, Uncaught Exception, Exposed Dangerous Method 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-19-134-08 Siemens SIMATIC…
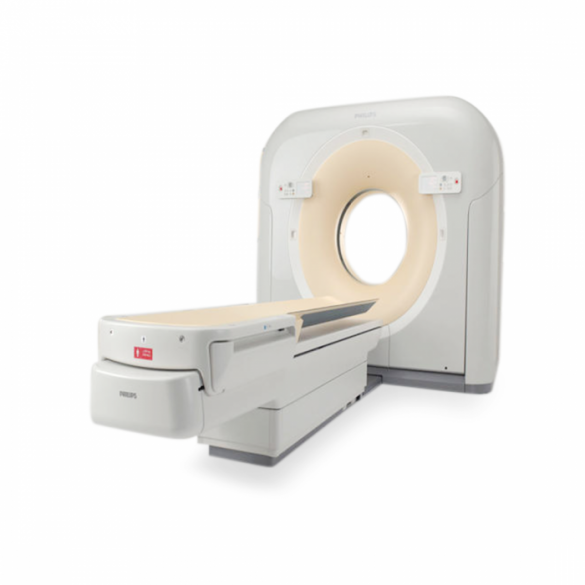
Philips Brilliance Computed Tomography (CT) System (Update A)
1. EXECUTIVE SUMMARY CVSS v3 8.4 ATTENTION: Low skill level to exploit Vendor: Philips ——— Begin Update A Part 1 of 3 ———- Equipment: Brilliance CT Scanners and MX8000 Dual EXP ——— End Update A Part 1 of 3 ———- Vulnerabilities: Execution with Unnecessary Privileges, Exposure of Resource to…
Siemens Industrial Products Local Privilege Escalation Vulnerability (Update I) Original release date: October 10, 2019
1. EXECUTIVE SUMMARY CVSS v3 6.4 ATTENTION: Exploitable locally Vendor: Siemens Equipment: Industrial Products Vulnerability: Improper privilege management 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory titled ICSA-16-313-02 Siemens Industrial Products Local Privilege Escalation Vulnerability (Update H) that was published June 14, 2018, on…
SMA Solar Technology AG Sunny WebBox
1. EXECUTIVE SUMMARY CVSS v3 9.6 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: SMA Solar Technology AG Equipment: Sunny WebBox Vulnerability: Cross-Site Request Forgery 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to generate a denial-of-service condition, modify passwords, enable services, achieve man-in-the-middle, and…
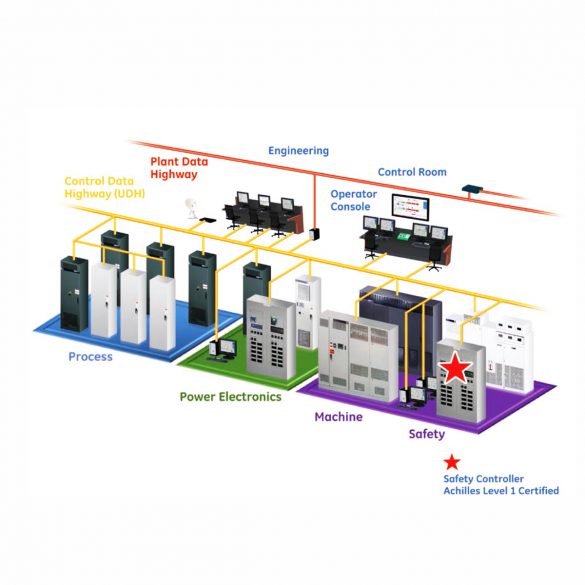
GE Mark VIe Controller
1. EXECUTIVE SUMMARY CVSS v3 6.8 ATTENTION: Low skill level to exploit Vendor: GE Equipment: Mark VIe Controller Vulnerabilities: Improper Authorization, Use of Hard-coded Credentials 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to create read/write/execute commands within the Mark VIe control system. 3. TECHNICAL…
Siemens SIMATIC WinAC RTX (F) 2010
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC WinAC RTX (F) 2010 Vulnerability: Uncontrolled Resource Consumption 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to perform a denial-of-service attack that could compromise the availability of the…






Stay connected