Advantech WebAccess/SCADA
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Advantech Equipment: WebAccess/SCADA Vulnerabilities: Improper Authentication, Authentication Bypass, SQL Injection 2. RISK EVALUATION Successful exploitation of these vulnerabilities may allow an attacker to access and manipulate sensitive data. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The…
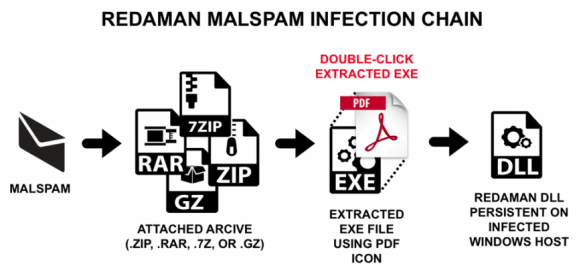
Russian Language Malspam Pushing Redaman Banking Malware
Redaman is banking malware first noted in 2015 that targets recipients who conduct transactions using Russian financial institutions. First reported as the RTM banking Trojan, vendors like Symantecand Microsoft described an updated version of this malware as Redaman in 2017. We have found versions of Redaman in Russian language…
Critical flaw in Linux APT package manager could allow remote hack
Expert discovered a remote code execution vulnerability in the APT package manager used by several Linux distributions, including Debian and Ubuntu. The independent security consultant Max Justicz has discovered a remote code execution vulnerability in the APT package manager used by several Linux distributions, including Debian and Ubuntu….
Johnson Controls Facility Explorer
1. EXECUTIVE SUMMARY CVSS v3 7.4 ATTENTION: Exploitable remotely Vendor: Johnson Controls Equipment: Facility Explorer Vulnerabilities: Path Traversal, Improper Authentication 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to read, write, and delete sensitive files to gain administrator privileges in the Facility Explorer system. 3….
Dräger Infinity Delta
1. EXECUTIVE SUMMARY CVSS v3 8.4 ATTENTION: Low skill level to exploit Vendor: Dräger Equipment: Infinity Delta Vulnerabilities: Improper Input Validation, Information Exposure Through Log Files, Improper Privilege Management 2. RISK EVALUATION Successful exploitation of these vulnerabilities could cause information disclosure of device logs, denial…
ControlByWeb X-320M
1. EXECUTIVE SUMMARY CVSS v3 7.6 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: ControlByWeb Equipment: X-320M Vulnerabilities: Improper Authentication, Cross-site Scripting 2. RISK EVALUATION Successful exploitation of these vulnerabilities may allow arbitrary code execution and could cause the device being accessed to require a physical factory reset to…
ABB CP400 Panel Builder TextEditor 2.0
1. EXECUTIVE SUMMARY CVSS v7.0 Vendor: ABB Equipment: CP400 Panel Builder TextEditor 2.0 Vulnerability: Improper Input Validation 2. RISK EVALUATION Successful exploitation of this vulnerability may allow an attacker to execute arbitrary code, and cause a denial-of-service condition within the Text Editor application. 3. TECHNICAL DETAILS 3.1 AFFECTED…
Omron CX-Supervisor
1. EXECUTIVE SUMMARY CVSS v3 7.3 ATTENTION: Low skill level to exploit Vendor: Omron Equipment: CX-Supervisor Vulnerabilities: Code Injection, Command Injection, Use After Free, Type Confusion 2. RISK EVALUATION Successful exploitation of these vulnerabilities could result in a denial-of-service condition, and/or allow an attacker to achieve code execution…
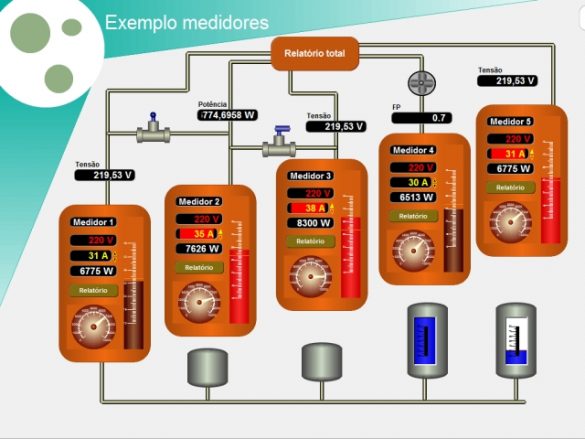
LCDS – Leão Consultoria e Desenvolvimento de Sistemas Ltda ME LAquis SCADA
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: LCDS – Leão Consultoria e Desenvolvimento de Sistemas Ltda ME Equipment: LAquis SCADA Vulnerabilities: Improper Input Validation, Out-of-Bounds Read, Code Injection, Untrusted Pointer Dereference, Out-of-Bounds Write, Relative Path Traversal, Injection, Use of Hard-Coded Credentials, Authentication…
36-Year-Old SCP Clients’ Implementation Flaws Discovered
A set of 36-year-old vulnerabilities has been uncovered in the Secure Copy Protocol (SCP) implementation of many client applications that can be exploited by malicious servers to overwrite arbitrary files in the SCP client target directory unauthorizedly. Session Control Protocol (SCP), also known as secure…







Stay connected