White hat hacker found a macOS Mojave privacy bypass 0-day flaw on release day
The popular macOS expert and former NSA hacker has discovered a zero-day vulnerability in macOS on Mojave ‘s release day. It is always Patrick Wardle, this time the popular expert and former NSA hacker has found a zero-day flaw in macOS on Mojave ‘s release…
Critical flaw affects Cisco Video Surveillance Manager
Cisco has patched a critical vulnerability in the Cisco Video Surveillance Manager (VSM) could be exploited by an unauthenticated remote attacker to gain root access. Cisco has fixed a critical vulnerability in the Cisco Video Surveillance Manager software running on some Connected Safety and Security…
Firefox DoS issue crashes the browser and sometimes the Windows OS
A security researcher discovered a bug affecting Firefox on Mac, Linux, and Windows that could crash the browser and in some cases the underlying OS. The security researcher Sabri Haddouche from Wire discovered a bug that affects Firefox on Mac, Linux, and Windows that could crash the browser and…
Researcher Discloses New Zero-Day Affecting All Versions of Windows
A security researcher has publicly disclosed an unpatched zero-day vulnerability in all supported versions of Microsoft Windows operating system (including server editions) after the company failed to patch a responsibly disclosed bug within the 120-days deadline. Discovered by Lucas Leong of the Trend Micro Security Research team,…
Cisco fixes Remote Code Execution flaws in Webex Network Recording Player
Cisco released security patches to fix RCE flaws in the Webex Network Recording Player for Advanced Recording Format (ARF). Cisco released security patches to address vulnerabilities in the Webex Network Recording Player for Advanced Recording Format (ARF) (CVE-2018-15414, CVE-2018-15421, and CVE-2018-15422) that could be exploited…
Zero-Day Bug Allows Hackers to Access CCTV Surveillance Cameras
Firmware used in up to 800,000 CCTV cameras open to attack thanks to buffer overflow zero-day bug. Between 180,000 and 800,000 IP-based closed-circuit television cameras are vulnerable to a zero-day vulnerability that allows hackers to access surveillance cameras, spy on and manipulate video feeds or…
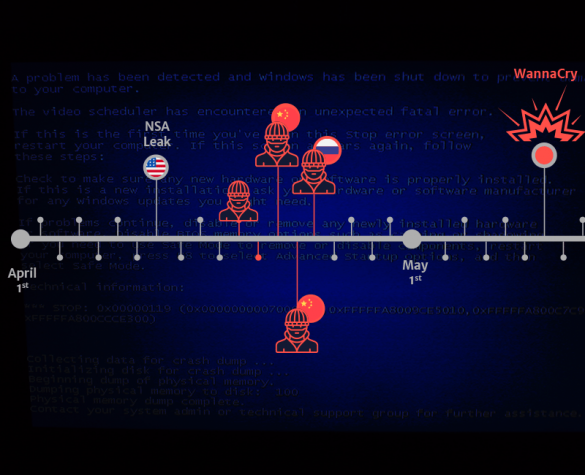
Cracked Windows installations are serially infected with EternalBlue exploit code
According to Avira, hundreds of thousands of unpatched Windows systems are serially infected with EternalBlue exploit code. The EternalBlue, is the alleged NSA exploit that made the headlines with DOUBLEPULSAR in the WannaCry attack. The malicious code was leaked online by the Shadow Brokers hacking group that stole it from the arsenal of the…
EOSBet Gambling application hacked, crooks stole $200,000 worth of EOS
The gambling application EOSBet was affected by a vulnerability in its smart contract system that has been exploited by attackers to steal $200,000 worth of EOS. The security breach was first reported by the member “thbourlove” of the EOSBet Reddit community that shared the code used to exploit the flaw. After…
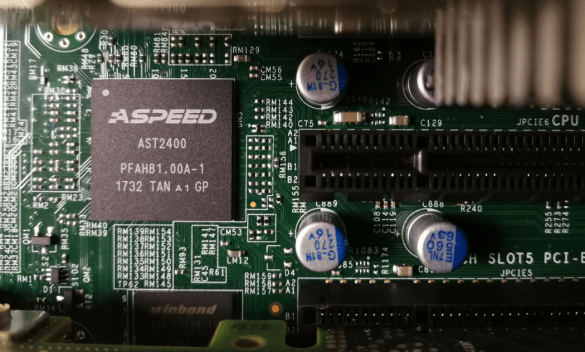
Flaw in update process for BMCs in Supermicro servers allows to deliver persistent malware or brick the server
A team of security researchers discovered a vulnerability in the baseboard management controller (BMC) hardware used by Supermicro servers. Researchers from security firm Eclypsium have discovered a vulnerability in the firmware update mechanism that could be exploited by hackers to deliver persistent malware, completely wipe and reinstall…
Philips e-Alert Unit
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit/exploitable from within the same local subnet Vendor: Philips Equipment: Philips e-Alert Unit (non-medical device) Vulnerabilities: Improper Input Validation, Cross-site Scripting, Information Exposure, Incorrect Default Permissions, Cleartext Transmission of Sensitive Information, Cross-site Request Forgery, Session Fixation, Resource…







Stay connected