GE S2020/S2020G Fast Switch 61850
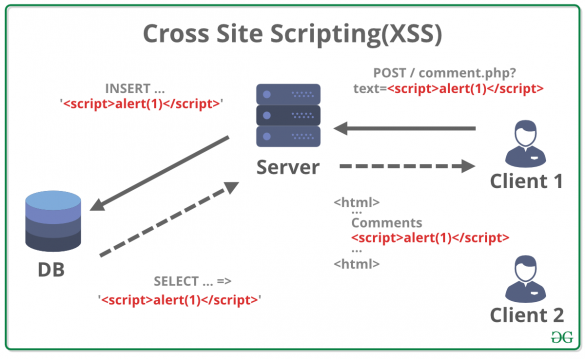
1. EXECUTIVE SUMMARY CVSS v3 4.6 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: GE Equipment: GE S2020/S2020G Fast Switch 61850 Vulnerability: Cross-site Scripting 2. RISK EVALUATION Successful exploitation of this vulnerability may allow an attacker to inject arbitrary code and allow disclosure of sensitive data. 3. TECHNICAL DETAILS…
Siemens SiNVR 3
1. EXECUTIVE SUMMARY CVSS v3 9.9 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SiNVR 3 Vulnerabilities: Cleartext Storage of Sensitive Information in GUI, Improper Authentication, Relative Path Traversal, Missing Authentication for Critical Function, Weak Cryptography for Passwords, Exposed Dangerous Method or Function 2. RISK EVALUATION Successful…
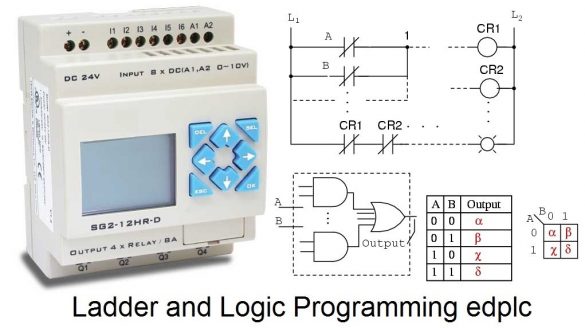
PLC Cycle Time Influences (Update A)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit/public exploits are available Vendors: ABB, Phoenix Contact, Schneider Electric, Siemens, WAGO Equipment: Programmable Logic Controllers Vulnerability: Uncontrolled Resource Consumption 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-19-106-03 PLC Cycle…
Siemens XHQ Operations Intelligence
1. EXECUTIVE SUMMARY CVSS v3 8.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: XHQ Operations Intelligence Vulnerabilities: Cross-site Request Forgery, Improper Neutralization of Script-Related HTML Tags in a Web Page, Improper Input Validation 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to…
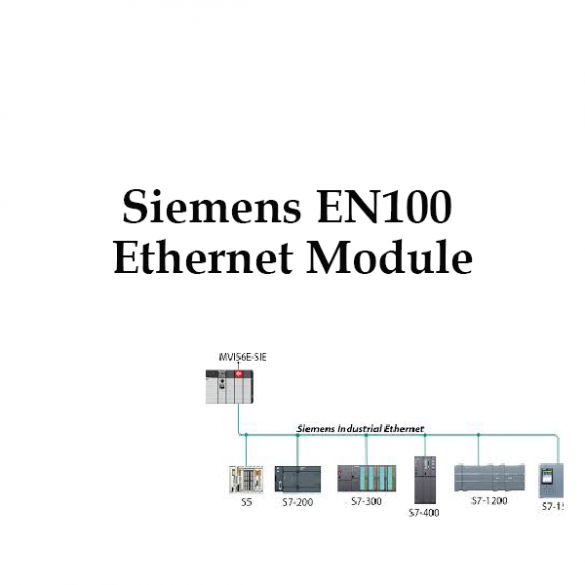
Siemens EN100 Ethernet Module
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: EN100 Ethernet Module Vulnerabilities: Improper Restriction of Operations within the Bounds of a Memory Buffer, Cross-site Scripting, Relative Path Traversal 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to…
Advantech DiagAnywhere Server
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Advantech Equipment: DiagAnywhere Server Vulnerability: Stack-based Buffer Overflow 2. RISK EVALUATION Successful exploitation of this vulnerability may allow remote code execution. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of DiagAnywhere Server, used for…
Siemens S7-1200 and S7-200 SMART CPUs (Update A)
. EXECUTIVE SUMMARY CVSS v3 6.8 ATTENTION: Low skill level to exploit Vendor: Siemens ——— Begin Update A Part 1 of 2 ——— Equipment: S7-1200 CPU family (including SIPLUS variants); S7-200 SMART CPU family ——— End Update A Part 1 of 2 ——— Vulnerability: Exposed Dangerous Method…
Interpeak IPnet TCP/IP Stack (Update B)
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit/public exploits are available Vendors: ENEA, Green Hills Software, ITRON, IP Infusion, Wind River Equipment: OSE by ENEA, INTEGRITY RTOS by Green Hills Software, ITRON, ZebOS by IP Infusion, and VxWorks by Wind River Vulnerabilities: Stack-based Buffer…
Siemens Industrial Products (Update C)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Industrial Products Vulnerabilities: Integer Overflow or Wraparound, Uncontrolled Resource Consumption 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory titled ICSA-19-253-03 Siemens Industrial Products (Update B) that was published…
Siemens SIPROTEC 5 and DIGSI 5 (Update B)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely; low skill level to exploit Vendor: Siemens Equipment: SIPROTEC 5 and DIGSI 5 Vulnerabilities: Improper Input Validation 2 UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-19-190-05 Siemens SIPROTEC 5 and DIGSI 5 (Update A) that…








Stay connected