Siemens SIMATIC WinAC RTX (F) 2010
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC WinAC RTX (F) 2010 Vulnerability: Uncontrolled Resource Consumption 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to perform a denial-of-service attack that could compromise the availability of the…
Siemens Industrial Products (Update A)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Industrial Products Vulnerabilities: Integer Overflow or Wraparound, Uncontrolled Resource Consumption 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-19-253-03 Siemens Industrial Products that was published September 10,…
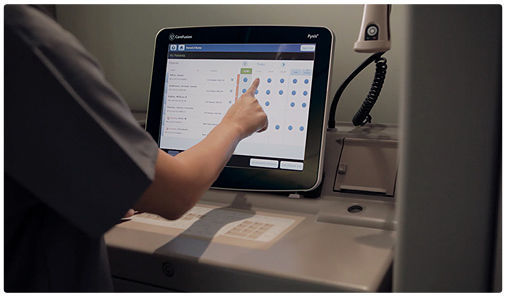
BD Pyxis (Update A)
1. EXECUTIVE SUMMARY CVSS v3 7.6 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Becton, Dickinson and Company (BD) Equipment: Pyxis Vulnerability: Session Fixation 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-19-248-01 BD Pyxis that was published September 5, 2019, on the…
Siemens CP, SIMATIC, SIMOCODE, SINAMICS, SITOP, and TIM (Update D)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: CP, SIMATIC, SIMOCODE, SINAMICS, SITOP, and TIM Vulnerability: Out-of-bounds Read 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory titled ICSA-19-099-06 Siemens CP, SIMATIC, SIMOCODE, SINAMICS, SITOP, and TIM…
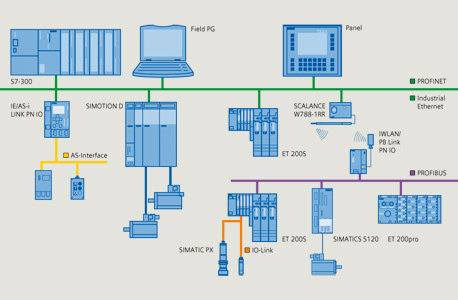
Siemens SIMATIC, SINUMERIK, and PROFINET IO (Update D)
1. EXECUTIVE SUMMARY CVSS v3 5.3 ATTENTION: Exploitable from an adjacent network Vendor: Siemens Equipment: SIMATIC, SINUMERIK, and PROFINET IO Vulnerability: Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-18-079-02 Siemens SIMATIC, SINUMERIK, and PROFINET IO (Update C) that was…
Siemens Industrial Products (Update N)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Remotely exploitable/low skill level to exploit Vendor: Siemens Equipment: Industrial Products Vulnerability: Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory titled ICSA-17-339-01 Siemens Industrial Products (Update M) published March…
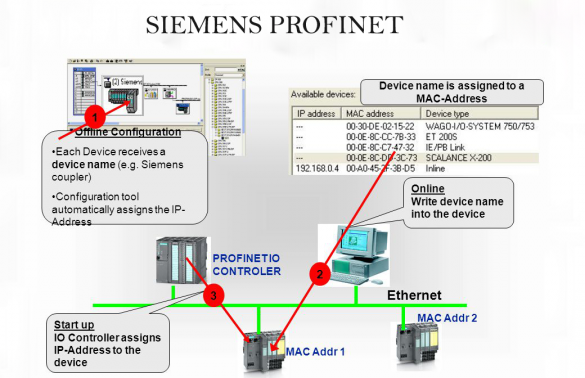
Siemens devices using the PROFINET Discovery and Configuration Protocol (Update P)
1. EXECUTIVE SUMMARY CVSS v3 6.5 ATTENTION: Exploitable from an adjacent network/low skill level to exploit. Vendor: Siemens Equipment: Devices using the PROFINET Discovery and Configuration Protocol (DCP) Vulnerabilities: Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory…
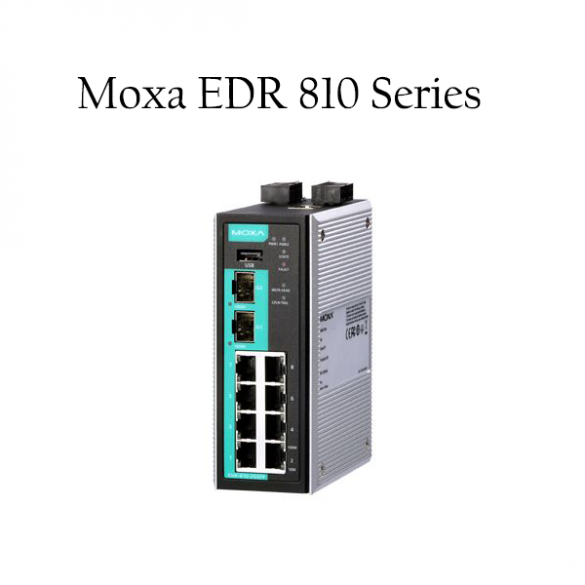
Moxa EDR 810 Series
1. EXECUTIVE SUMMARY CVSS v3 7.2 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Moxa Equipment: EDR 810 Vulnerabilities: Improper Input Validation, Improper Access Control 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow remote code execution or access to sensitive information. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS…
Yokogawa Products
1. EXECUTIVE SUMMARY CVSS v3 8.4 ATTENTION: Low skill level to exploit Vendor: Yokogawa Equipment: Exaopc, Exaplog, Exaquantum, Exasmoc, Exarqe, GA10, and InsightSuiteAE Vulnerability: Unquoted Search Path or Element 2. RISK EVALUATION Successful exploitation of this vulnerability could allow a local attacker to execute malicious files. 3. TECHNICAL DETAILS…
Interpeak IPnet TCP/IP Stack
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit/public exploits are available Vendors: ENEA, Green Hills Software, ITRON, IP Infusion, Wind River Equipment: OSE by ENEA, INTEGRITY RTOS by Green Hills Software, ITRON, Zebos by IP Infusion, and VxWorks by Wind River Vulnerabilities: Stack-based Buffer…





Stay connected