DTLS “ClientHello” Race Conditions in WebRTC Implementations
AbstractThis research uncovers a security flaw in WebRTC implementations, urging developers to enforce stricter source verification for DTLS ClientHello packets to prevent denial of service attacks.Introduction to WebRTCWeb Real‑Time Communication (WebRTC) is a technology that enables peer‑to‑peer communication directly between web browsers or mobile applications….
Distributed Energy Resources Cybersecurity Outlook:Vulnerabilities, Attacks, Impacts, and Mitigations
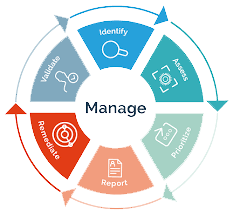
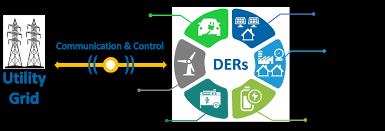
Abstract—The digitization and decentralization of the electric power grid are key thrusts for an economically and environmentally sustainable future. Towards this goal, distributed energy resources (DER), including rooftop solar panels, battery storage, electric vehicles, etc., are becoming ubiquitous in power systems. Power utilities benefit from…
POWER OUT?
SOLARINVERTERS AND THESILENT CYBER THREAT What’s the problem? As Australia accelerates adoption of renewable energy sources, new cyber securityvulnerabilities are being introduced through Internet of Things (IoT) devices. Cyber securityconcerns about these devices, notably photovoltaic inverters (solar inverters), have recentlycome to the fore, and policy…
GhostRace: Exploiting and Mitigating Speculative Race Conditions
Race conditions arise when multiple threads attempt to ac- cess a shared resource without proper synchronization, often leading to vulnerabilities such as concurrent use-after-free. To mitigate their occurrence, operating systems rely on syn- chronization primitives such as mutexes, spinlocks, etc. In this paper, we present…
NFC RELAY ATTACK ON TESLA MODEL Y
This paper will walk you through the proof-of-concept and technical details of exploitation forIOActive’s recent NFC relay attack on the newest Tesla vehicle, the Model Y.To successfully carry out the attack, IOActive reverse-engineered the NFC protocol Tesla usesbetween the NFC card and the vehicle, and…
The KeyTrap Denial-of-Service Algorithmic Complexity Attacks on DNSVersion: January 2024
Abstract—Availability is a major concern in the design of DNSSEC. To ensure availability, DNSSEC follows Postel’s Law [RFC1122]: ”Be liberal in what you accept, and conservative inwhat you send.” Hence, nameservers should send not just one matching key for a record set, but all the…
Passive SSH Key Compromise via Lattices
ABSTRACTWe demonstrate that a passive network attacker can opportunistically obtain private RSA host keys from an SSH server that experiences a naturally arising fault during signature computation. In prior work, this was not believed to be possible for the SSH protocol because the signature included…
Terrapin Attack: Breaking SSH Channel IntegrityBy Sequence Number Manipulation
Abstract The SSH protocol provides secure access to network services, particularly remote terminal login and file transfer within organizational networks and to over 15 million servers on the open internet. SSH uses an authenticated key exchange to establish a secure channel between a client and…
Windows API Exploitation in Real World By Akash Sarode
Cyber Security in today’s world has become more challenging thantraditional days where we had Firewall and antivirus as our main defensesystems. Modern day adversary have got all the necessary resources – (Time,Team & Money) to execute their tasks of getting a victim compromised. Mostof the…
BLUFFS: Bluetooth Forward and Future Secrecy Attacks andDefenses
ABSTRACTBluetooth is a pervasive technology for wireless communication.Billions of devices use it in sensitive applications and to exchangeprivate data. The security of Bluetooth depends on the Bluetoothstandard and its two security mechanisms: pairing and session establishment. No prior work, including the standard itself, analyzed the…








Stay connected