ZF Roll Stability Support Plus (RSSPlus)
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an unauthenticated attacker to remotely (proximal/adjacent with RF equipment) call diagnostic functions which could impact both the availability and integrity. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of RSSPlus are…
Siemens SIMATIC S7-1200 CPUs
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an unauthenticated attacker to change the CPU mode by tricking a legitimate and authenticated user with sufficient permissions on the target CPU to click on a malicious link. 3. TECHNICAL DETAILS 3.1…
Cisco NX-OS Software Image Verification Bypass Vulnerability
Summary A vulnerability in the bootloader of Cisco NX-OS Software could allow an unauthenticated attacker with physical access to an affected device, or an authenticated, local attacker with administrative credentials, to bypass NX-OS image signature verification. This vulnerability is due to insecure bootloader settings. An…
DTLS “ClientHello” Race Conditions in WebRTC Implementations
AbstractThis research uncovers a security flaw in WebRTC implementations, urging developers to enforce stricter source verification for DTLS ClientHello packets to prevent denial of service attacks.Introduction to WebRTCWeb Real‑Time Communication (WebRTC) is a technology that enables peer‑to‑peer communication directly between web browsers or mobile applications….
Bosch Rexroth IndraDrive
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to cause a denial-of-service, rendering the device unresponsive by sending arbitrary UDP messages. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Bosch Rexroth reports that the following versions of IndraDrive, servo drive…
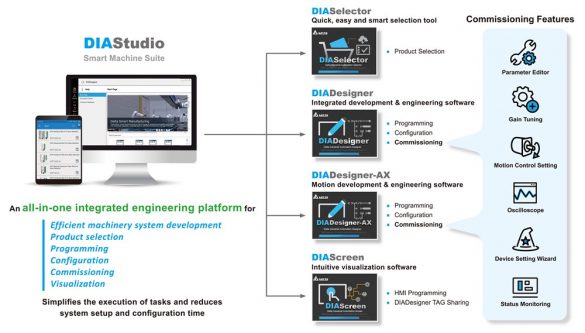
Delta Electronics DIAScreen
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this these vulnerabilities could crash the device being accessed; a buffer overflow condition may allow remote code execution. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of DIAScreen, which is a component of Delta’s DIAStudio…
LiteSpeed Cache Plugin Vulnerability Poses Significant Risk to WordPress Websites
A high-severity security flaw has been disclosed in the LiteSpeed Cache plugin for WordPress that could allow an unauthenticated threat actor to elevate their privileges and perform malicious actions. The vulnerability, tracked as CVE-2024-50550 (CVSS score: 8.1), has been addressed in version 6.5.2 of the…
Delta Electronics InfraSuite Device Master
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an unauthenticated attacker to remotely execute arbitrary code. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of InfraSuite Device Master, a real-time device monitoring software, are affected: 3.2 Vulnerability Overview 3.2.1 DESERIALIZATION…
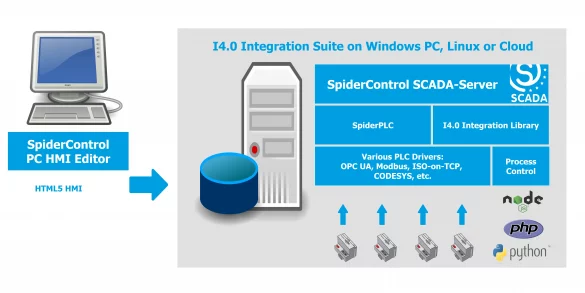
iniNet Solutions SpiderControl SCADA PC HMI Editor
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to gain remote control of the device. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of iniNet Solutions SpiderControl SCADA PC HMI Editor, a software management platform, are affected:…
VIMESA VHF/FM Transmitter Blue Plus
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to perform a Denial-of-Service. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following version of VIMESA VHF/FM Transmitter Blue Plus, a VHF/FM Transmitter, is affected: 3.2 Vulnerability Overview 3.2.1 Improper Access Control…








Stay connected