Mitsubishi Electric MELSEC and MELIPC Series (Update A)
1. EXECUTIVE SUMMARY 2. UPDATE INFORMATION This updated advisory is a follow up to the original advisory titled ICSA-21-334-02 Mitsubishi Electric MELSEC and MELIPC Series that was published on November 30, 2021, to the ICS webpage on www.cisa.gov/uscert. 3. RISK EVALUATION Successful exploitation of these…
GE Gas Power ToolBoxST
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low attack complexity Vendor: GE Gas Power Equipment: ToolBoxST Vulnerabilities: Improper Restriction of XML External Entity Reference, Path Traversal 2. RISK EVALUATION Successful exploitation of these vulnerabilities could result in data exfiltration or arbitrary write, overwrite, and execution. 3. TECHNICAL DETAILS…
Geutebrück G-Cam E2 and G-Code
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low attack complexity/public exploits are available Vendor: Geutebrück Equipment: G-Cam E2 and G-Code Vulnerabilities: Missing Authentication for Critical Function, Command Injection, Stack-based Buffer Overflow 2. RISK EVALUATION UDP Technology supplies multiple OEMs such as Geutebrück with firmware for IP cameras. Successful…
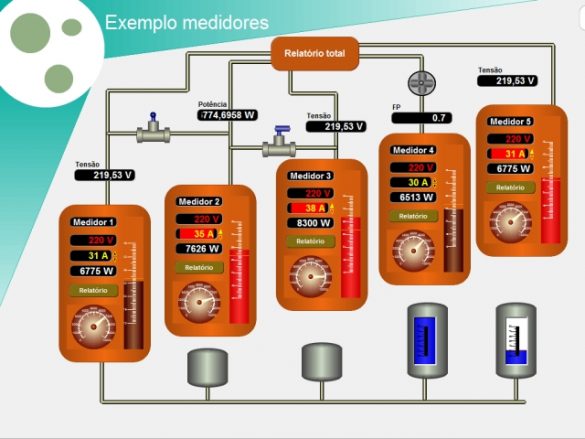
LCDS LAquis SCADA
1. EXECUTIVE SUMMARY CVSS v3 9.3 ATTENTION: Exploitable remotely/low attack complexity Vendor: LCDS—Leão Consultoria e Desenvolvimento de Sistemas Ltda ME Equipment: LAquis SCADA Vulnerability: Cross-site Scripting 2. RISK EVALUATION Successful exploitation of this vulnerability may allow an unauthenticated remote attacker to access sensitive information or execute arbitrary code. 3….
Delta Electronics DIAScreen
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low attack complexity Vendor: Delta Electronics Equipment: DIAScreen Vulnerabilities: Type Confusion, Out-of-bounds Write 2. RISK EVALUATION Successful exploitation of these vulnerabilities could crash the device being accessed and may allow remote code execution. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions…
Delta Electronics DOPSoft (Update A)
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low attack complexity Vendor: Delta Electronics Equipment: DOPSoft Vulnerabilities: Out-of-bounds Read 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-21-182-03 Delta Electronics DOPSoft that was published July 1, 2021, on the ICS webpage on us-cert.cisa.gov. 3….
Mitsubishi Electric GOT (Update A)
1. EXECUTIVE SUMMARY CVSS v3 5.9 ATTENTION: Exploitable remotely Vendor: Mitsubishi Electric Equipment: GOT Vulnerability: Improper Authentication 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-21-112-02 Mitsubishi Electric GOT that was published April 22, 2021, on the ICS webpage on us-cert.cisa.gov. 3. RISK EVALUATION…
Mitsubishi Electric Factory Automation Engineering Products (Update D)
1. EXECUTIVE SUMMARY CVSS v3 8.3 ATTENTION: Exploitable remotely Vendor: Mitsubishi Electric Equipment: Mitsubishi Electric, Factory Automation Engineering products Vulnerability: Unquoted Search Path or Element 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-20-212-04 Mitsubishi Electric Factory Automation Engineering Products (Update C) that…
Mitsubishi Electric MELSEC-F Series
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low attack complexity Vendor: Mitsubishi Electric Equipment: MELSEC-F Series Vulnerability: NULL Pointer Dereference 2. RISK EVALUATION Successful exploitation of this vulnerability may cause a denial-of-service condition in communication with the product. System reset may be required for recovery. 3. TECHNICAL DETAILS…
Ypsomed mylife
1. EXECUTIVE SUMMARY CVSS v3 6.3 ATTENTION: Exploitable remotely/low attack complexity Vendor: Ypsomed Equipment: mylife Cloud, mylife Mobile Application Vulnerabilities: Insufficiently Protected Credentials, Not Using an Unpredictable IV with CBC Mode, Use of Hard-coded Credentials 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to obtain…









Stay connected