Hitachi ABB Power Grids AFS Series
1. EXECUTIVE SUMMARY Hitachi ABB Power Grids AFS Series CVSS v3 6.5 ATTENTION: Low skill level to exploit Vendor: Hitachi ABB Power Grids Equipment: AFS Series Vulnerability: Infinite Loop 2. RISK EVALUATION Successful exploitation of this vulnerability could cause a denial-of-service condition on one of the ports in a…
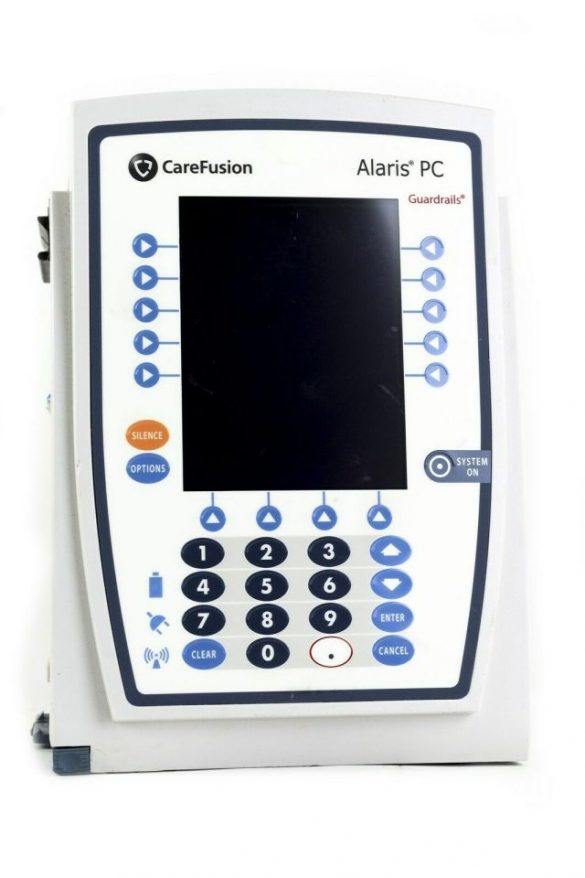
BD Alaris 8015 PC Unit (Update B)
1. EXECUTIVE SUMMARY CVSS v3 6.8 ATTENTION: Low skill level to exploit Vendor: Becton, Dickinson and Company (BD) Equipment: BD Alaris 8015 PC Unit Vulnerabilities: Insufficiently Protected Credentials, Security Features 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSMA-17-017-02 BD Alaris 8015 Insufficiently…
Schneider Electric IGSS SCADA Software
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low skill level to exploit Vendor: Schneider Electric Equipment: IGSS (Interactive Graphical SCADA System) Vulnerabilities: Improper Restriction of Operations within the Bounds of a Memory Buffer 2. RISK EVALUATION Successful exploitation of these vulnerabilities could result in remote code execution. 3. TECHNICAL…
Siemens Solid Edge File Parsing
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low skill level to exploit Vendor: Siemens Equipment: Solid Edge Vulnerabilities: Out-of-bounds Write, Improper Restriction of XML External Entity Reference, Out-of-bounds Read 2. RISK EVALUATION Successful exploitation of these vulnerabilities could lead to a denial-of-service condition, and could lead to arbitrary code…
Luxion KeyShot (Update A)
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low skill level to exploit Vendor: Luxion Equipment: KeyShot products Vulnerabilities: Out-of-bounds Write, Out-of-bounds Read, Insufficient UI Warning of Dangerous Operations, Untrusted Pointer Dereference, Path Traversal 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-21-035-01 Luxion…
TCP/IP Stack Vulnerabilities–AMNESIA:33 in SENTRON PAC / 3VA Devices
1. EXECUTIVE SUMMARY CVSS v3 6.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SENTRON 3VA COM100/800, SENTRON 3VA DSP800, SENTRON PAC2200, SENTRON PAC3200T, SENTRON PAC3200, SENTRON PAC3220, SENTRON PAC4200 Vulnerabilities: Out-of-bounds Read, Out-of-bounds Write 2. RISK EVALUATION Successful exploitation of these vulnerabilities could cause a denial-of-service…
Siemens TCP Stack of SIMATIC MV400
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC MV400 Vulnerabilities: Improper Validation of Specified Index, Position, or Offset in Input; Use of Insufficiently Random Values 2. RISK EVALUATION Successful exploitation of these vulnerabilities could cause a denial-of-service condition or affect…
Siemens Energy PLUSCONTROL 1st Gen
1. EXECUTIVE SUMMARY CVSS v3 6.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: PLUSCONTROL Vulnerability: Predictable Exact Value from Previous Values 2. RISK EVALUATION Successful exploitation of this vulnerability could affect integrity of TCP connections. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Siemens reports the vulnerability affects…
dnsmasq by Simon Kelley (Update A)
1. EXECUTIVE SUMMARY CVSS v3 8.1 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: dnsmasq by Simon Kelley Equipment: dnsmasq Vulnerabilities: Heap-based Buffer Overflow, Insufficient Verification of Data Authenticity, Use of a Broken or Risky Cryptographic Algorithm CISA is aware of a public report, known as “DNSpooq” that details…
Siemens UMC Stack (Update F)
1. EXECUTIVE SUMMARY CVSS v3 6.7 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: UMC Stack Vulnerabilities: Unquoted Search Path or Element, Uncontrolled Resource Consumption, Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-20-196-05 Siemens UMC Stack (Update…






Stay connected