Siemens SIMATIC, SINAMICS, SINEC, SINEMA, SINUMERIK (Update F)
1. EXECUTIVE SUMMARY CVSS v3 6.7 ATTENTION: Low skill level to exploit Vendor: Siemens Equipment: SIMATIC, SINAMICS, SINEC, SINEMA, SINUMERIK Vulnerability: Unquoted Search Path or Element 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-20-161-04 Siemens SIMATIC, SINAMICS, SINEC, SINEMA, SINUMERIK (Update D)…
Siemens KTK, SIDOOR, SIMATIC, and SINAMICS (UpdateB)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: KTK, SIDOOR, SIMATIC, and SINAMICS Vulnerability: Uncontrolled Resource Consumption 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-20-105-08 Siemens KTK, SIDOOR, SIMATIC, and SINAMICS (Update A) that…
Siemens PROFINET-IO Stack (Update D)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Siemens PROFINET-IO Stack Vulnerability: Uncontrolled Resource Consumption 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-20-042-04 Siemens PROFINET-IO Stack (Update C) that was published February 9, 2021,…
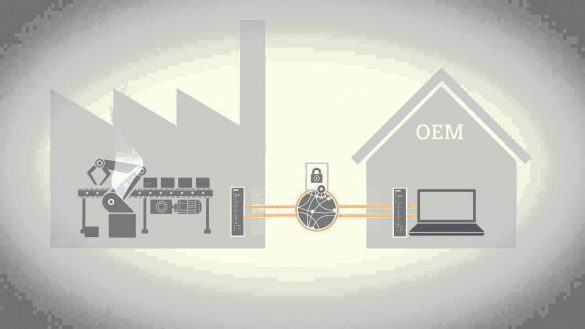
Siemens SINEMA Remote Connect (Update A)
1. EXECUTIVE SUMMARY CVSS v3 8.3 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SINEMA Remote Connect (Client and Server) Vulnerabilities: Incorrect Calculation of Buffer Size, Out-of-bounds Read, Stack-based Buffer Overflow, Improper Handling of Insufficient Permissions 2. UPDATE INFORMATION This updated advisory is a follow-up to the…
Siemens Industrial Products (Update Q)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Remotely exploitable/low skill level to exploit Vendor: Siemens Equipment: Industrial Products Vulnerability: Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory titled ICSA-17-339-01 Siemens Industrial Products (Update P) published August 11,…
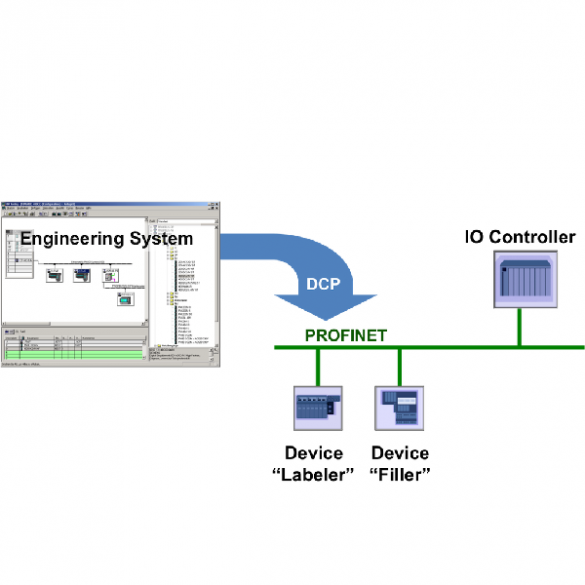
Siemens PROFINET DCP (Update S)
1. EXECUTIVE SUMMARY CVSS v3 6.5 ATTENTION: Exploitable from an adjacent network/low skill level to exploit. Vendor: Siemens Equipment: Devices using the PROFINET Discovery and Configuration Protocol (DCP) Vulnerabilities: Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory…
Rockwell Automation 1734-AENTR Series B and Series C
1. EXECUTIVE SUMMARY CVSS v3 7.5 Rockwell Automation 1734-AENTR Series B and Series C ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Rockwell Automation Equipment: 1734-AENTR Series B and Series C Vulnerabilities: Improper Access Control, Cross-site Scripting 2. RISK EVALUATION Successful exploitation of these vulnerabilities could lead to unauthorized…
Schneider Electric EcoStruxure Building Operation (EBO)
1. EXECUTIVE SUMMARY CVSS v3 6.7 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Schneider Electric Equipment: EcoStruxure Building Operation Vulnerabilities: Unrestricted Upload of File with Dangerous Type, Cross-site Scripting, Improper Restriction of XML External Entity Reference, Improper Access Control, Windows Unquoted Search Path 2. RISK EVALUATION Successful exploitation…
Hitachi ABB Power Grids Ellipse EAM
1. EXECUTIVE SUMMARY CVSS v3 5.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Hitachi ABB Power Grids Equipment: Ellipse EAM Vulnerabilities: Cross-site Scripting, User Interface Misrepresentation of Critical Information 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to steal sensitive information, hijack a user’s…
MB connect line mbCONNECT24, mymbCONNECT24
1. EXECUTIVE SUMMARY MB connect line mbCONNECT24, mymbCONNECT24 CVSS v3 7.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: MB connect line Equipment: mymbCONNECT24, mbCONNECT24 Vulnerabilities: MB Improper Privilege Management, Server-side Request Forgery (SSRF), Cross-site Scripting, Uncontrolled Resource Consumption, Open Redirect, Insecure Default Initialization of Resource, PHP Remote File…








Stay connected