Siemens SIMATIC HMI Products
1. EXECUTIVE SUMMARY CVSS v3 6.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC HMI Vulnerabilities: Improper Restriction of Excessive Authentication Attempts, Authentication Bypass by Primary Weakness 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow a remote attacker to discover user passwords and obtain…
Wibu-Systems CodeMeter
1. EXECUTIVE SUMMARY CVSS v3 10.0 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Wibu-Systems AG Equipment: CodeMeter Vulnerabilities: Buffer Access with Incorrect Length Value, Inadequate Encryption Strength, Origin Validation Error, Improper Input Validation, Improper Verification of Cryptographic Signature, Improper Resource Shutdown or Release 2. UPDATE INFORMATION This updated…
Siemens UMC Stack (Update B)
1. EXECUTIVE SUMMARY CVSS v3 6.7 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: UMC Stack Vulnerabilities: Unquoted Search Path or Element, Uncontrolled Resource Consumption, Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-20-196-05 Siemens UMC Stack (Update…
Siemens SIMATIC, SINAMICS, SINEC, SINEMA, SINUMERIK (Update C)
1. EXECUTIVE SUMMARY CVSS v3 6.7 ATTENTION: Low skill level to exploit Vendor: Siemens Equipment: SIMATIC, SINAMICS, SINEC, SINEMA, SINUMERIK Vulnerability: Unquoted Search Path or Element 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-20-161-04 Siemens SIMATIC, SINAMICS, SINEC, SINEMA, SINUMERIK (Update B)…
Siemens RUGGEDCOM, SCALANCE, SIMATIC, SINEMA (Update B)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: RUGGEDCOM, SCALANCE, SIMATIC, SINEMA Vulnerabilities: Uncontrolled Resource Consumption, Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-20-105-05 Siemens IE/PB-Link, RUGGEDCOM, SCALANCE, SIMATIC, SINEMA…
Siemens SCALANCE & SIMATIC (Update B)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SCALANCE, SIMATIC Vulnerability: Resource Exhaustion 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-20-105-07 Siemens SCALANCE & SIMATIC (Update A) that was published August 11, 2020, to…
Siemens SIMATIC PCS 7, SIMATIC WinCC, and SIMATIC NET PC (Update E)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC PCS 7, SIMATIC WinCC, SIMATIC NET PC Vulnerability: Incorrect Calculation of Buffer Size 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled 20-042-06 Siemens SIMATIC PCS 7,…
Siemens PROFINET Devices (Update H)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: PROFINET Devices Vulnerability: Uncontrolled Resource Consumption 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-19-283-02 Siemens PROFINET Devices (Update G) that was published August 11, 2020, to…
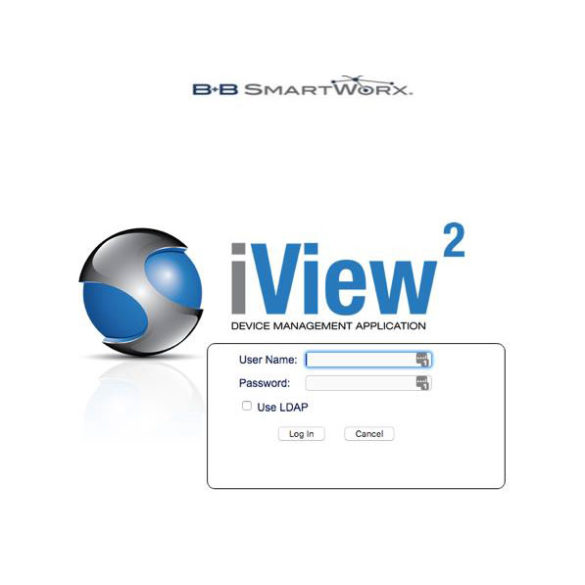
Advantech iView
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Advantech Equipment: iView Vulnerability: Path Traversal 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to read/modify information, execute arbitrary code, limit system availability, and/or crash the application. 3. TECHNICAL DETAILS 3.1…
Emerson OpenEnterprise
1. EXECUTIVE SUMMARY CVSS v3 3,8 ATTENTION: Low skill level to exploit Vendor: Emerson Equipment: OpenEnterprise SCADA Software Vulnerability: Inadequate Encryption Strength 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker access to credentials held by OpenEnterprise used for accessing field devices and external systems. 3….










Stay connected