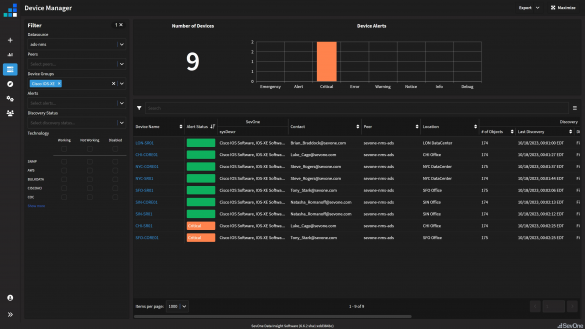
CISA Releases Guidance for Addressing Cisco IOS XE Web UI Vulnerabilities
SummaryCisco has provided an update regarding the ongoing investigation into the observed exploitation of the web UI feature in Cisco IOS XE Software. The initial fixed software releases are now available on the Cisco Software Download Center. Cisco will continue to update the advisory as…
Siemens SIMATIC Cloud Connect 7
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to execute arbitrary code. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following products from Siemens are affected: 3.2 VULNERABILITY OVERVIEW 3.2.1 IMPROPER NEUTRALIZATION OF SPECIAL ELEMENTS USED IN A COMMAND (‘COMMAND…
Siemens RADIUS Client of SIPROTEC 5 Devices
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low attack complexity Vendor: Siemens ProductCERT Equipment: RADIUS client of SIPROTEC 5 devices Vulnerability: Loop with Unreachable Exit Condition (‘Infinite Loop’) 2. RISK EVALUATION The RADIUS client implementation of the VxWorks platform in SIPROTEC 5 devices contains a denial-of-service vulnerability that…
Siemens SIMATIC Industrial Products
1. EXECUTIVE SUMMARY CVSS v3 7.9 ATTENTION: Low attack complexity Vendor: Siemens Equipment: SIMATIC industrial products Vulnerability: Time-of-check Time-of-use (TOCTOU) Race Condition 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow a privileged user to potentially enable escalation of privilege via local access. 3. TECHNICAL DETAILS 3.1 AFFECTED…
Mitsubishi Electric MELSOFT iQ AppPortal
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low attack complexity Vendor: Mitsubishi Electric Equipment: MELSOFT iQ AppPortal Vulnerabilities: HTTP Request Smuggling, Insufficient Verification of Data Authenticity 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow a malicious attacker to make unidentified impacts such as authentication bypass, information…
Johnson Controls System Configuration Tool (SCT)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely Vendor: Johnson Controls Equipment: System Configuration Tool Vulnerabilities: Sensitive Cookie Without ‘HttpOnly’ Flag, Sensitive Cookie in HTTPS Session Without ‘Secure’ Attribute 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to access cookies and take over the…
Fortinet Releases Security Updates for FortiOS
Fortinet has released security updates to address a heap-based buffer overflow vulnerability (CVE-2022-42475) in FortiOS. An attacker could exploit this vulnerability to take control of an affected system. FortiOS – heap-based buffer overflow in sslvpnd Summary A heap-based buffer overflow vulnerability [CWE-122] in FortiOS SSL-VPN may…
Cradlepoint IBR600
1. EXECUTIVE SUMMARY CVSS v3 7.1 ATTENTION: Low attack complexity Vendor: Cradlepoint Equipment: IBR600 Vulnerabilities: Command Injection 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to execute code and native system commands. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of Cradlepoint IBR600 are…
CISCO Identity Services Engine Unauthorized File Access Vulnerability
A vulnerability in the web-based management interface of Cisco Identity Services Engine (ISE) could allow an authenticated, remote attacker to read and delete files on an affected device.This vulnerability is due to insufficient validation of user-supplied input. An attacker could exploit this vulnerability by sending…
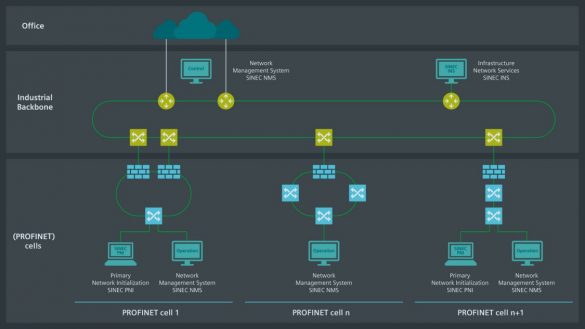
Siemens SINEC INS
1. EXECUTIVE SUMMARY CVSS v3 8.8 ATTENTION: Exploitable remotely/Low attack complexity Vendor: Siemens Equipment: SINEC INS Vulnerabilities: Improper Input Validation, Integer Overflow or Wraparound, Uncontrolled Resource Consumption, Command Injection, Inadequate Encryption Strength, Missing Encryption of Sensitive Data, Improper Restriction of Operations Within the Bounds of a Memory Buffer, Exposure…








Stay connected