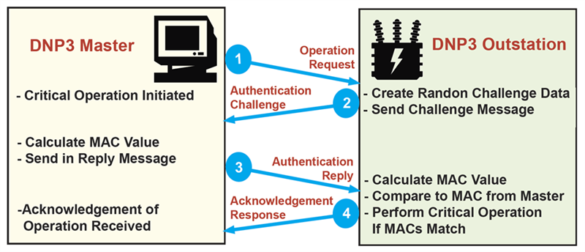
Triangle MicroWorks DNP3 Outstation Libraries
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Triangle MicroWorks Equipment: DNP3 Outstation Libraries Vulnerability: Stacked-based Buffer Overflow 2. RISK EVALUATION Successful exploitation of this vulnerability could possibly allow remote attackers to stop the execution of code on affected equipment. 3. TECHNICAL DETAILS…
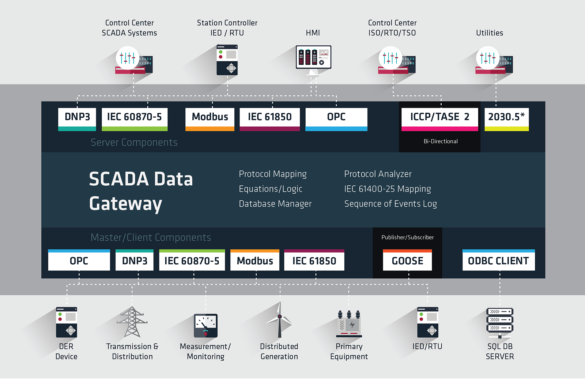
Triangle MicroWorks SCADA Data Gateway
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Triangle MicroWorks Equipment: SCADA Data Gateway Vulnerabilities: Stacked-based Buffer Overflow, Out-of-Bounds Read, Type Confusion 2. RISK EVALUATION These vulnerabilities allow remote attackers to execute arbitrary code and disclose on affected installations…
Siemens Climatix
1. EXECUTIVE SUMMARY CVSS v3 6.1 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Climatix Vulnerability: Cross-site Scripting, Basic XSS 2. RISK EVALUATION Successful exploitation of this vulnerability could allow a remote attacker to execute arbitrary code to access confidential information without authentication. 3. TECHNICAL DETAILS 3.1…
Siemens IE/PB-Link, RUGGEDCOM, SCALANCE, SIMATIC, SINEMA
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: IE/PB-Link, RUGGEDCOM, SCALANCE, SIMATIC, SINEMA Vulnerabilities: Uncontrolled Resource Consumption, Improper Input Validation 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow remote attackers to affect the availability of the devices under certain…
Siemens SIMOTICS, Desigo, APOGEE, and TALON
1. EXECUTIVE SUMMARY CVSS v3 7.1 ATTENTION: Exploitable from an adjacent network/low skill level to exploit Vendor: Siemens Equipment: SIMOTICS, Desigo, APOGEE, and TALON Vulnerability: Business Logic Errors 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to affect the availability and integrity of the device….
Siemens SCALANCE & SIMATIC
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SCALANCE, SIMATIC Vulnerability: Resource Exhaustion 2. RISK EVALUATION Successful exploitation of this vulnerability can result in a denial-of-service condition. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of SCALANCE are affected: SCALANCE…
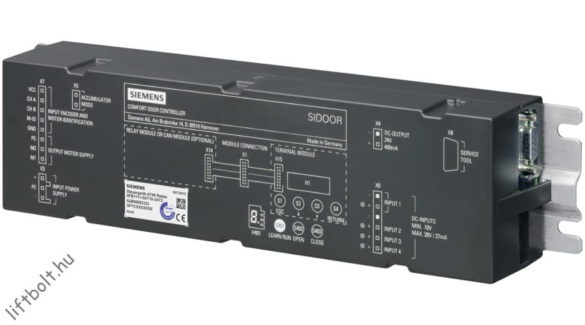
Siemens KTK, SIDOOR, SIMATIC, and SINAMICS
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: KTK, SIDOOR, SIMATIC, and SINAMICS Vulnerability: Uncontrolled Resource Consumption 2. RISK EVALUATION Successful exploitation of this vulnerability could create a denial-of-service condition. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following Siemens products are…
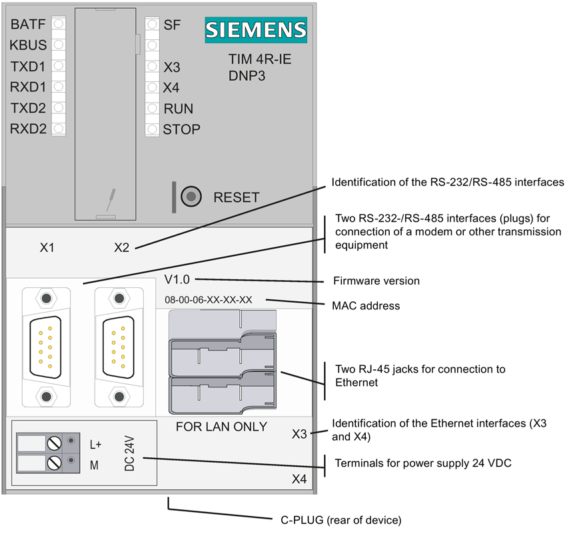
Siemens TIM 3V-IE and 4R-IE Family Devices
1. EXECUTIVE SUMMARY CVSS v3 9.0 ATTENTION: Exploitable remotely Vendor: Siemens Equipment: TIM 3V-IE and 4R-IE Family Devices Vulnerability: Active Debug Code 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an unauthenticated attacker with network access to gain full control over the device. 3. TECHNICAL DETAILS 3.1 AFFECTED…
Siemens SIMATIC S7 (Update B)
1. EXECUTIVE SUMMARY CVSS v3 5.3 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC S7 Vulnerability: Uncontrolled Resource Consumption (Resource Exhaustion) 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-20-042-05 Siemens SIMATIC S7 (Update A) that was published March 10,…
Siemens TIA Portal (Update A)
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low skill level to exploit Vendor: Siemens Equipment: TIA Portal Vulnerability: Path Traversal 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-20-014-05 Siemens TIA Portal that was published January 14, 2020, to the ICS webpage on…





Stay connected