Siemens Industrial Products (Update F)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Industrial Products Vulnerabilities: Integer Overflow or Wraparound, Uncontrolled Resource Consumption 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory titled ICSA-19-253-03 Siemens Industrial Products (Update E) that was published…
Rockwell Automation RSLinx Classic
1. EXECUTIVE SUMMARY CVSS v3 8.8 ATTENTION: Low skill level to exploit Vendor: Rockwell Automation Equipment: RSLinx Classic Vulnerability: Incorrect Permission Assignment for Critical Resource 2. RISK EVALUATION Successful exploitation of this vulnerability could allow a local authenticated attacker to execute malicious code when opening RSLinx Classic. 3. TECHNICAL…
BD Pyxis MedStation and Pyxis Anesthesia (PAS) ES System
1. EXECUTIVE SUMMARY CVSS v3 6.8 ATTENTION: Low skill level to exploit Vendor: Becton, Dickinson and Company (BD) Equipment: Pyxis MedStation and Pyxis Anesthesia (PAS) ES System Vulnerability: Protection Mechanism Failure 2. RISK EVALUATION The affected BD medical devices utilize a method of software application implementation called “kiosk mode.”…
Advantech WebAccess/NMS
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Advantech Equipment: WebAccess/NMS Vulnerabilities: Unrestricted Upload of File with Dangerous Type, SQL Injection, Relative Path Traversal, Missing Authentication for Critical Function, Improper Restriction of XML External Entity Reference, OS Command Injection 2. RISK EVALUATION Successful…
GE Digital CIMPLICITY
1. EXECUTIVE SUMMARY CVSS v3 6.0 ATTENTION: Low skill level to exploit Vendor: GE Digital Equipment: CIMPLICITY Vulnerability: Improper Privilege Management 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an adversary to modify the systemwide CIMPLICITY configuration, leading to the arbitrary execution of code. 3. TECHNICAL DETAILS…
HMS Networks eWON Flexy and Cosy
1. EXECUTIVE SUMMARY CVSS v3 6.1 ATTENTION: Exploitable remotely Vendor: HMS Networks Equipment: eWON Flexy and Cosy Vulnerability: Cross-site Scripting 2. RISK EVALUATION Successful exploitation of this vulnerability could initiate a password change. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following eWON products are affected: eWON Flexy: All firmware…
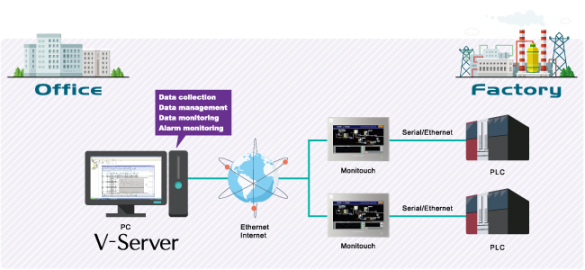
Fuji Electric V-Server Lite
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Fuji Electric Equipment: V-Server Lite Vulnerability: Heap-based Buffer Overflow 2. RISK EVALUATION Successful exploitation of this vulnerability could allow a remote attacker to gain elevated privileges for remote code execution. 3. TECHNICAL DETAILS 3.1 AFFECTED…
B&R Automation Studio
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: B&R Automation Equipment: Automation Studio Vulnerabilities: Improper Privilege Management, Missing Required Cryptographic Step, Path Traversal 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to delete arbitrary files from this system, fetch…
KUKA.Sim Pro
1. EXECUTIVE SUMMARY CVSS v3 4.3 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: KUKA Equipment: Sim Pro Vulnerability: Improper Enforcement of Message Integrity During Transmission in a Communication Channel 2. RISK EVALUATION Successful exploitation of this vulnerability could result in a loss of integrity in external 3D models…
Synergy Systems & Solutions HUSKY RTU (Update A)
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Synergy Systems & Solutions (SSS) Equipment: HUSKY RTU ——— Begin Update A Part 1 of 3 ——— Vulnerabilities: Improper Authentication, Improper Input Validation, Missing Authentication for Critical Function, Improper Check for Unusual or Exceptional…









Stay connected