Siemens SIMATIC Products (Update B)
1. EXECUTIVE SUMMARY CVSS v3.1 3.7 ATTENTION: Exploitable remotely Vendor: Siemens Equipment: SIMATIC CP 1626; HMI Panel (incl. SIPLUS variants); NET PC software; STEP 7 (TIA Portal); WinCC (TIA Portal); WinCC OA; WinCC Runtime (Pro and Advanced); TIM 1531 IRC (incl. SIPLUS variant) Vulnerability: Exposed Dangerous Method or Function…
Siemens SIMATIC S7-1200 and S7-1500 CPU Families (Update A)
1. EXECUTIVE SUMMARY CVSS v3 5.3 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC S7-1200 and S7-1500 CPU families Vulnerabilities: Use of a Broken or Risky Cryptographic Algorithm, Missing Support for Integrity Check 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory…
Siemens Industrial Real-Time (IRT) Devices (Update C)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Industrial Real-Time (IRT) Devices Vulnerability: Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-19-283-01 Siemens Industrial Real-Time (IRT) Devices (Update B) that was published…
Siemens PROFINET Devices (Update D)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: PROFINET Devices Vulnerability: Uncontrolled Resource Consumption 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-19-283-02 Siemens PROFINET Devices (Update C) that was published February 11, 2020, to…
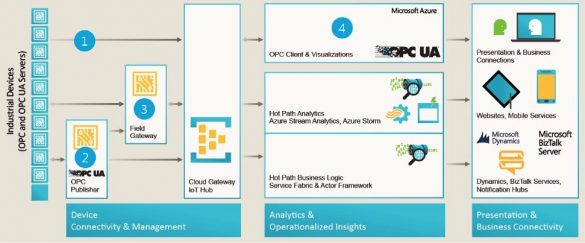
Siemens Industrial Products with OPC UA (Update F)
1. EXECUTIVE SUMMARY CVSS v3.1 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC, SINEC-NMS, SINEMA, SINEMURIK Industrial Control Products with OPC UA Vulnerability: Uncaught Exception 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory titled ICSA-19-099-03 Siemens Industrial Products with OPC…
Siemens Industrial Products with OPC UA (Update F)
1. EXECUTIVE SUMMARY CVSS v3.1 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC, SINEC-NMS, SINEMA, SINEMURIK Industrial Control Products with OPC UA Vulnerability: Uncaught Exception 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory titled ICSA-19-099-03 Siemens Industrial Products with OPC…
Siemens SIMATIC, SIMOCODE, SINAMICS, SITOP, and TIM (Update G)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC, SIMOCODE, SINAMICS, SITOP, and TIM Vulnerability: Out-of-bounds Read 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory titled ICSA-19-099-06 Siemens SIMATIC, SIMOCODE, SINAMICS, SITOP, and TIM (Update F)…
Siemens S7-300/400 PLC Vulnerabilities (Update E)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC S7-300 and SIMATIC S7-400 Vulnerabilities: Information Exposure, Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-16-348-05 SIEMENS S7-300/400 PLC Vulnerabilities (Update D) that…
Emerson ValveLink
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low skill level to exploit Vendor: Emerson Equipment: ValveLink Vulnerability: Improper Access Control 2. RISK EVALUATION Successful exploitation of this vulnerability could allow arbitrary code execution. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of ValveLink digital valve controller software are…
PHOENIX CONTACT Emalytics Controller ILC
1. EXECUTIVE SUMMARY CVSS v3 9.4 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Phoenix Contact Equipment: Emalytics Controller ILC 2050 BI(L) Vulnerability: Incorrect Permission Assignment for Critical Resource 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to change the device configuration and start or…








Stay connected