Siemens CP, SIMATIC, SIMOCODE, SINAMICS, SITOP, and TIM (Update E)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: CP, SIMATIC, SIMOCODE, SINAMICS, SITOP, and TIM Vulnerability: Out-of-bounds Read 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory titled ICSA-19-099-06 Siemens CP, SIMATIC, SIMOCODE, SINAMICS, SITOP, and TIM…
Siemens SCALANCE X Switches, RUGGEDCOM WiMAX, RFID 181-EIP, and SIMATIC RF182C (Update C)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable from the same local network segment (OSI Layer 2) Vendor: Siemens Equipment: SCALANCE X switches, RUGGEDCOM Win, RFID 181-EIP, and SIMATIC RF182C Vulnerability: Heap-based Buffer Overflow 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-18-165-01…
Siemens SCALANCE X Switches (Update A)
1. EXECUTIVE SUMMARY CVSS v3 5.8 ATTENTION: Exploitable remotely Vendor: Siemens Equipment: SCALANCE X switches Vulnerabilities: Cross-site Scripting 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-18-163-02 Siemens SCALANCE X Switches that was published June 12, 2018, on the ICS webpage on us-cert. 3….
Potential for Iranian Cyber Response to U.S. Military Strike in Baghdad
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit/public exploits are available Vendors: ENEA, Green Hills Software, ITRON, IP Infusion, Wind River Equipment: OSE by ENEA, INTEGRITY RTOS by Green Hills Software, ITRON, ZebOS by IP Infusion, and VxWorks by Wind River Vulnerabilities: Stack-based Buffer…
Omron CX-Supervisor (Update A)
1. EXECUTIVE SUMMARY CVSS v3 8.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Omron Equipment: CX-Supervisor Vulnerability: Use of Obsolete Function 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-19-318-04 Omron CX-Supervisor that was published November 14, 2019, on the ICS webpage…
Equinox Control Expert
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Equinox Equipment: Control Expert Vulnerability: Improper Neutralization of Special Elements used in an SQL Command (‘SQL Injection’) 2. RISK EVALUATION Successful exploitation of this vulnerability may allow remote code execution. 3. TECHNICAL DETAILS 3.1 AFFECTED…
Reliable Controls MACH-ProWebCom/Sys
1. Reliable Controls MACH-ProWebCom/Sys EXECUTIVE SUMMARY CVSS v3 8.2 ATTENTION: Exploitable remotely Vendor: Reliable Controls Equipment: MACH-ProWebCom/Sys Vulnerability: Cross-site Scripting 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to execute commands on behalf of the affected user. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following…
AVEVA Vijeo Citect and Citect SCADA (Update A)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit ——— Begin Update A Part 1 of 5 ——— Vendor: AVEVA and Schneider Electric Equipment: AVEVA’s Vijeo Citect and Citect SCADA; Schneider Electric’s Power SCADA Operation ——— End Update A Part 1 of 5 ———…
Philips IntelliBridge EC40/80 (Update A)
1. EXECUTIVE SUMMARY CVSS v3 6.3 ATTENTION: Low skill level to exploit Vendor: Philips Equipment: IntelliBridge EC40 and EC80 Vulnerability: Inadequate Encryption Strength 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSMA-19-318-01 Philips IntelliBridge EC40/80 that was published November 14, 2019, on the…
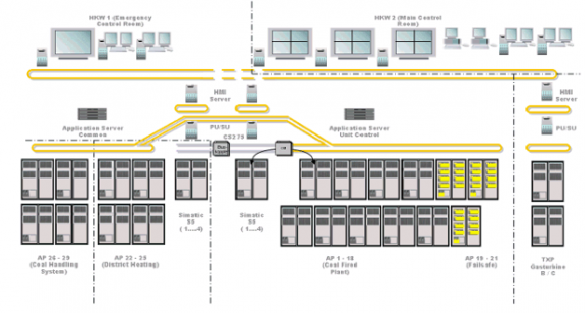
Siemens SPPA-T3000
1. Siemens SPPA-T3000-EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SPPA-T3000 Vulnerabilities: Improper Authentication, Cleartext Transmission of Sensitive Information, Unrestricted Upload of File with Dangerous Type, Heap-based Buffer Overflow, Integer Overflow or Wraparound, Out-of-bounds Read, Improper Access Control, Stack-based Buffer Overflow, SFP…










Stay connected