Medtronic Conexus Radio Frequency Telemetry Protocol
. EXECUTIVE SUMMARY CVSS v9.3 ATTENTION: Exploitable with adjacent access/low skill level to exploit Vendor: Medtronic Equipment: MyCareLink Monitor, CareLink Monitor, CareLink 2090 Programmer, specific Medtronic implanted cardiac devices listed below Vulnerabilities: Improper Access Control, Cleartext Transmission of Sensitive Information 2. RISK EVALUATION Successful exploitation of these vulnerabilities may…
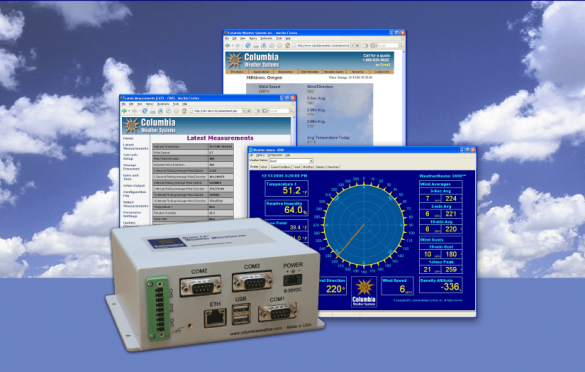
Columbia Weather Systems MicroServer
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Columbia Weather Systems, Inc. Equipment: Weather MicroServer Vulnerabilities: Cross-site Scripting, Path Traversal, Improper Authentication, Improper Input Validation, Code Injection 2. RISK EVALUATION Successful exploitation of these vulnerabilities may allow disclosure of data, cause a denial-of-service…
AVEVA InduSoft Web Studio and InTouch Edge HMI
1. EXECUTIVE SUMMARY CVSS v3 6.5 ATTENTION: Low skill level to exploit Vendor: AVEVA Equipment: InduSoft Web Studio, InTouch Edge HMI Vulnerability: Uncontrolled Search Path Element 2. RISK EVALUATION Successful exploitation of this vulnerability could allow execution of unauthorized code or commands. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The…
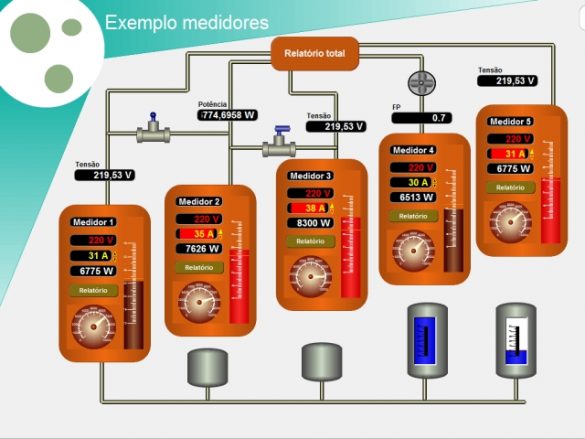
LCDS – Leão Consultoria e Desenvolvimento de Sistemas Ltda ME LAquis SCADA ELS Files
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low skill level to exploit Vendor: LCDS—Leão Consultoria e Desenvolvimento de Sistemas LTDA ME Equipment: LAquis SCADA Vulnerability: Out-of-Bounds Write 2. RISK EVALUATION Successful exploitation of this vulnerability could allow remote code execution. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following version…
Gemalto Sentinel UltraPro
1. EXECUTIVE SUMMARY CVSS v3 6.5 ATTENTION: Low skill level to exploit Vendor: Gemalto Equipment: Sentinel UltraPro Vulnerability: Uncontrolled Search Path Element 2. RISK EVALUATION Successful exploitation of this vulnerability could allow execution of unauthorized code or commands. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of Sentinel…
PEPPERL+FUCHS WirelessHART-Gateways
1. EXECUTIVE SUMMARY CVSS v3 5.3 ATTENTION: Exploitable remotely/low skill level to exploit/public exploits are available Vendor: PEPPERL+FUCHS Equipment: WirelessHART-Gateways Vulnerability: Path Traversal 2. RISK EVALUATION Successful exploitation of this vulnerability could allow access to files and restricted directories stored on the device through the manipulation of file parameters….
Siemens Industrial Products (Update M)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Remotely exploitable/low skill level to exploit Vendor: Siemens Equipment: Industrial Products Vulnerability: Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the updated advisory titled ICSA-17-339-01 Siemens Industrial Products (Update L) published February 12,…
Siemens Desigo PXC (Update C)
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Desigo PXC Vulnerability: Improper Authentication 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-18-025-02B Siemens Desigo PXC that was published March 22, 2018, on the NCCIC/ICS-CERT website….
Siemens SIPROTEC 4, SIPROTEC Compact, DIGSI 4, and EN100 Ethernet Module (Update C)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIPROTEC 4, SIPROTEC Compact, DIGSI 4, and EN100 Ethernet module Vulnerabilities: Missing Authentication for Critical Function, Inadequate Encryption Strength 2. UPDATE INFORMATION This updated advisory is a follow-up to…
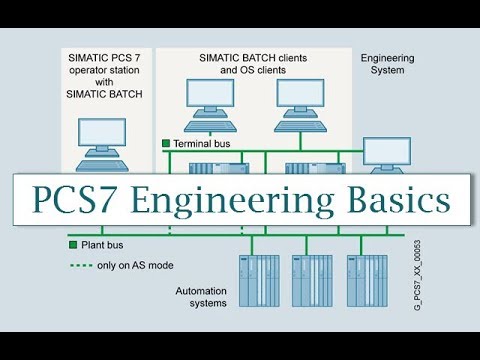
Siemens SIMATIC PCS 7, SIMATIC WinCC, SIMATIC WinCC Runtime Professional, and SIMATIC NET PC Software (Update G)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit. Vendor: Siemens Equipment: SIMATIC PCS 7, SIMATIC WinCC, SIMATIC WinCC Runtime Professional, and SIMATIC NET PC Software Vulnerability: Improper Input Validation 2. UPDATE INFORMATION This updated advisory is a follow-up to the…








Stay connected