Researchers from Trustwave SpiderLabs discovered an unpatched kernel-level vulnerability in driver used by IBM Trusteer Rapport endpoint security tool.
The issue affects endpoint security tool for MacOS, IBM released a patch but failed to address the vulnerability within the 120-day disclosure deadline.
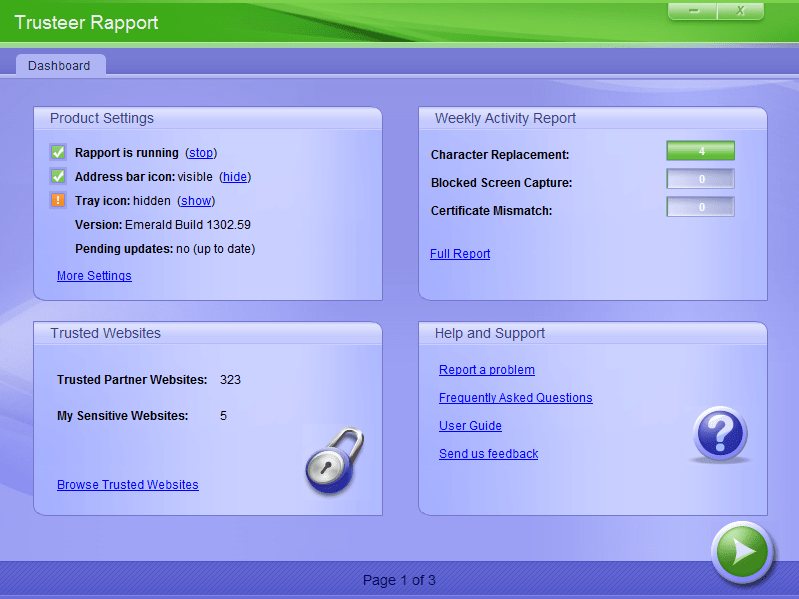
The IBM Trusteer Rapport endpoint security tool is a lightweight software component that locks down the user browser once he connects to a sensitive website. Any malicious software that tries to ride on the browser is left out of the locked down browser, and cannot access sensitive information and transactions.
Researchers from Trustwave SpiderLabs discovered a signedness bug in the handling of user-supplied buffers on a driver used by Trusteer Rapport on MacOS. The bug can lead to a memory corruption vulnerability in the Apple MacOS kernel and, subsequently, arbitrary code execution in the kernel.
“The vulnerability is a signedness bug leading to a Kernel stack memory corruption issue in a call to memcpy. IBM Trusteer Rapport is security software advertised as an additional layer of security to anti-virus software.” reads the analysis published by Trustwave SpiderLabs.
“The root cause of the issue is a signedness bug in validating the user-supplied number of elements provided by the user in the structure passed to the Kernel driver function via a call to an struct method exported from the Kernel driver with the IOService ‘com_trusteer_rapportke_v2’. “
Experts first reported the flaw to IBM on August 15 and helped the company in addressing it. They waited for 90-days according to their disclosure policy before disclosing the bug.
Trustwave granted IBM an additional 30 days and when that deadline was passed without releasing the patch, Trustwave publicly disclosed the flaw.
Fortunately, the vulnerability can be exploited only by a local attack, but experts pointed out that chaining the flaw with other issue attackers could obtain arbitrary code execution within the context of the kernel.
“Although there is currently no patch, the risk of this vulnerability is slightly mitigated by requiring local access, so those affected are recommended to verify that only authorized users can log in to those systems.” concludes the analysis. “Security awareness training can also help prevent local malware or social engineering attacks. Finally, you may want to step up auditing of any affected systems for signs of infection.”
Below the timeline for the vulnerability:
08/15/2018 – Vulnerability disclosed to vendor
11/13/2018 – 90-day deadline passed
11/14/2018 – Provided vendor 30-day extension for fix
12/17/2018 – Vendor confirms no patch is available
12/20/2018 – Advisory published
Source:
https://securityaffairs.co/wordpress/79141/hacking/kernel-buffer-overflow-trusteer-rapport.html

Stay connected