1. EXECUTIVE SUMMARY
- CVSS v3 6.5
- ATTENTION: Exploitable from an adjacent network/low attack complexity
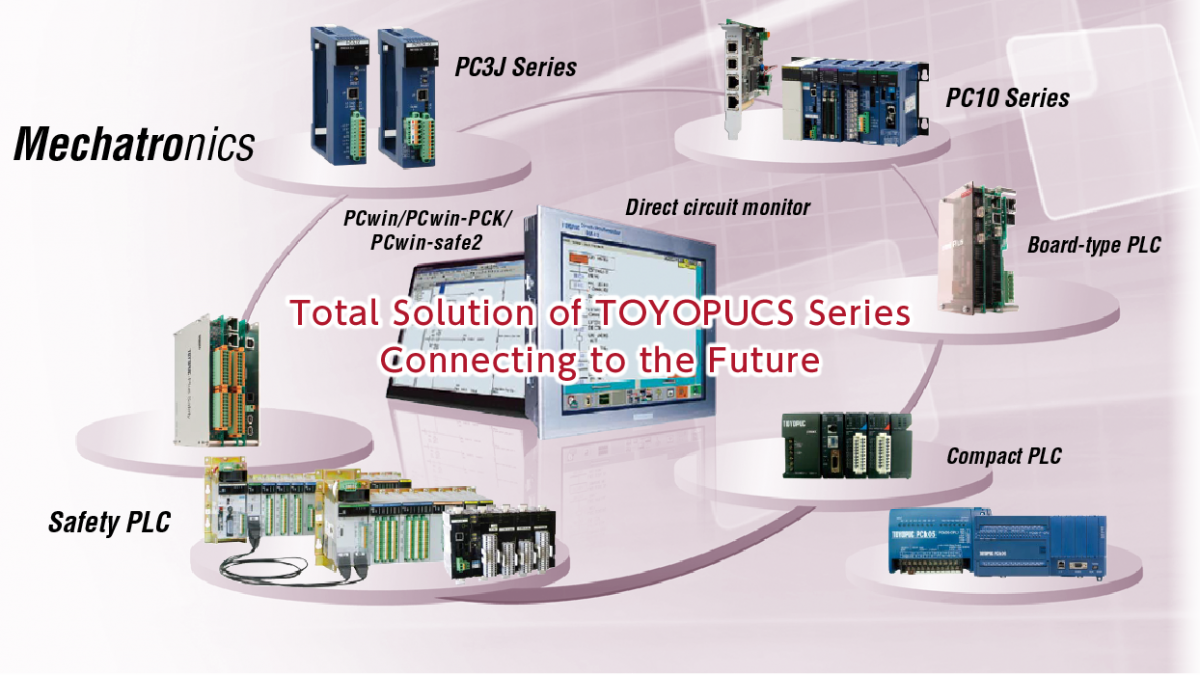
- Vendor: JTEKT Corporation
- Equipment: TOYOPUC PLC
- Vulnerability: Improper Restriction of Operations within the Bounds of a Memory Buffer
2. RISK EVALUATION
Successful exploitation of this vulnerability could crash the device being accessed.
3. TECHNICAL DETAILS
3.1 AFFECTED PRODUCTS
The following versions of the PLC are affected:
- PC10G-CPU
- 2PORT-EFR
- Plus CPU
- Plus EX
- Plus EX2
- Plus EFR
- Plus EFR2
- Plus 2P-EFR
- PC10P-DP
- PC10P-DP-IO
- Plus BUS-EX
- Nano 10GX
- Nano 2ET
- PC10PE
- PC10PE-16/16P
- PC10E
- FL/ET-T-V2H
- PC10B
- PC10B-P
- Nano CPU
- PC10P
- PC10GE
3.2 VULNERABILITY OVERVIEW
3.2.1 IMPROPER RESTRICTION OF OPERATIONS WITHIN THE BOUNDS OF A MEMORY BUFFER CWE-119
When the affected products receive an invalid frame, the outside area of a receive buffer for FL-net are overwritten. As a result, the PLC CPU detects a system error, and the affected products stop.
CVE-2021-27477 has been assigned to this vulnerability. A CVSS v3 base score of 6.5 has been calculated; the CVSS vector string is (AV:A/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H).
3.3 BACKGROUND
- CRITICAL INFRASTRUCTURE SECTORS: Critical Manufacturing
- COUNTRIES/AREAS DEPLOYED: Worldwide
- COMPANY HEADQUARTERS LOCATION: Japan
3.4 RESEARCHER
Chris Yang of TXOne Networks, working with Trend Micro’s Zero Day Initiative, reported this vulnerability to CISA.
4. MITIGATIONS
JTEKT has updated to the following PLC firmware versions to address the vulnerability:
- PC10G-CPU: Versions 3.91 or later
- 2PORT-EFR: Versions 1.50 or later
- PC10P-DP: Versions 1.50 or later
- PC10P-DP-IO: Versions 1.50 or later
- Nano 10GX: Versions 3.00 or later
- Nano 2ET: Versions 2.40 or later
- PC10PE: Versions 1.02 or later
- PC10PE-16/16P: Versions 1.02 or later
- PC10E: Versions 1.12 or later
- FL/ET-T-V2H: Versions F2.8 E1.5 or later
- PC10B: Versions 1.11 or later
- PC10B-P: Versions 1.11 or later
- Nano CPU: Versions 2.08 or later
- PC10P: Versions 1.05 or later
- PC10GE: Versions 1.04 or later
PLUS SERIES
- Plus CPU: Versions 3.11 or later
- Plus EX: Versions 3.11 or later
- Plus EX2: Versions 3.11 or later
- Plus EFR: Versions 3.11 or later
- Plus EFR2: Versions 3.11 or later
- Plus 2P-EFR: Versions 3.11 or later
- Plus BUS-EX: Version 2.13 or later
There is no need to update Plus series expansion boards. If you use a Plus series expansion board, update Plus CPU or Plus BUS-EX to which the expansion board is connected.
For firmware updates, visit the JTEKT website.
As a general security measure, JTEKT Corporation recommends users only build networks with trusted FL-net products.
Requests for additional information can be sent to JTEKT Corporation via website form.
CISA recommends users take defensive measures to minimize the risk of exploitation of this vulnerability. CISA reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures.
CISA also provides a section for control systems security recommended practices on the ICS webpage on us-cert.cisa.gov. Several recommended practices are available for reading and download, including Improving Industrial Control Systems Cybersecurity with Defense-in-Depth Strategies.
Additional mitigation guidance and recommended practices are publicly available on the ICS webpage on us-cert.cisa.gov in the Technical Information Paper, ICS-TIP-12-146-01B–Targeted Cyber Intrusion Detection and Mitigation Strategies.
Organizations observing any suspected malicious activity should follow their established internal procedures and report their findings to CISA for tracking and correlation against other incidents.
No known public exploits specifically target this vulnerability.
Source:

Stay connected