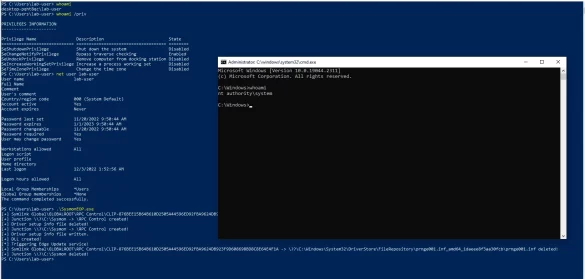
CVE-2022-41120 PoC released for Windows Sysmon Elevation of Privilege Vulnerability
A security researcher has published details and proof-of-concept (PoC) code for a Microsoft Windows Sysmon vulnerability that could be exploited to gain elevated privileges on the system. Tracked as CVE-2022-41120 (CVSS score of 7.8), the security defect was identified and reported in June, with a…
Mitsubishi Electric MELSEC iQ-R Series
1. EXECUTIVE SUMMARY CVSS v3 8.6 ATTENTION: Exploitable remotely/low attack complexity Vendor: Mitsubishi Electric Equipment: MELSEC iQ-R Series Vulnerability: Improper Input Validation 2. RISK EVALUATION Successful exploitation of this vulnerability could allow a remote unauthenticated attacker to cause a denial-of-service condition on a target product by sending specially crafted…
SIEMENS SINEC NETWORK MANAGEMENT SYSTEM LOGBACK COMPONENT
1. EXECUTIVE SUMMARY CVSS v3 6.6 ATTENTION: Exploitable remotely Vendor: Siemens Equipment: SINEC NMS Vulnerability: Deserialization of Untrusted Data 2. RISK EVALUATION Successful exploitation of this vulnerability could allow attackers with write access to the logback configuration file to execute arbitrary code on the system. 3. TECHNICAL DETAILS…
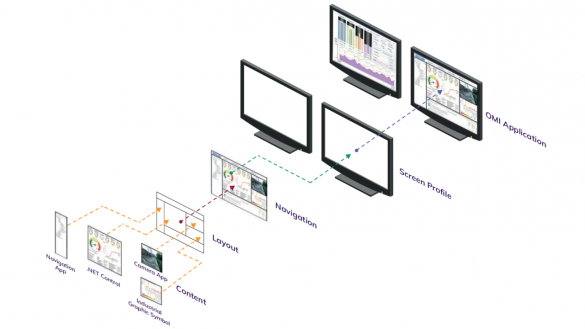
Mitsubishi Electric GT SoftGOT2000
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low attack complexity Vendor: Mitsubishi Electric Corporation Equipment: GT SoftGOT2000 Vulnerability: Operating System (OS) Command Injection 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to execute malicious OS commands. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Mitsubishi Electric…
AVEVA Edge
1. EXECUTIVE SUMMARY CVSS v3 4.7 ATTENTION: Exploitable remotely/low attack complexity/public exploits are available Vendor: Digital Alert Systems Equipment: DASDEC Vulnerability: Cross-site Scripting 2. RISK EVALUATION Successful exploitation of these vulnerabilities might result in false alerts being issued to broadcast or cable sites that are immediately connected to the…
Cradlepoint IBR600
1. EXECUTIVE SUMMARY CVSS v3 7.1 ATTENTION: Low attack complexity Vendor: Cradlepoint Equipment: IBR600 Vulnerabilities: Command Injection 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to execute code and native system commands. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of Cradlepoint IBR600 are…
Cisco Identity Services Engine Cross-Site Scripting Vulnerability
A vulnerability in the External RESTful Services (ERS) API of Cisco Identity Services Engine (ISE) Software could allow an authenticated, remote attacker to conduct a cross-site scripting (XSS) attack against a user of the interface of an affected device. This vulnerability is due to insufficient…
Cisco Releases Security Updates for Identity Services Engine
Cisco has released security updates for vulnerabilities affecting Cisco Identity Services Engine (ISE). A remote attacker could exploit some of these vulnerabilities to bypass authorization and access system files. CISA encourages users and administrators to review the following advisories and apply the necessary updates: Cisco…
Apple Releases Security Update for Xcode
Apple has released a security update to address vulnerabilities in Xcode. A remote attacker could exploit one of these vulnerabilities to take control of an affected system. About Apple security updates For our customers’ protection, Apple doesn’t disclose, discuss, or confirm security issues until an…
Nokia ASIK AirScale System Module
1. EXECUTIVE SUMMARY CVSS v3 8.4 ATTENTION: Low attack complexity Vendor: Nokia Equipment: ASIK AirScale 5G Common System Module Vulnerabilities: Improper Access Control for Volatile Memory Containing Boot Code, Assumed-Immutable Data is Stored in Writable Memory 2. RISK EVALUATION Successful exploitation of these vulnerabilities could result in the execution…








Stay connected