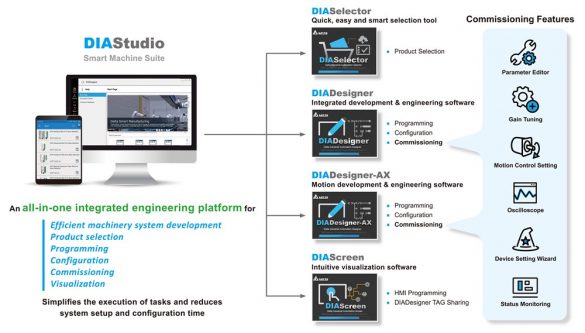
Delta Electronics DIAScreen
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to cause a stack-based buffer overflow, resulting in execution of arbitrary code. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions of Delta Electronics DIAScreen visualization software are affected: 3.2…
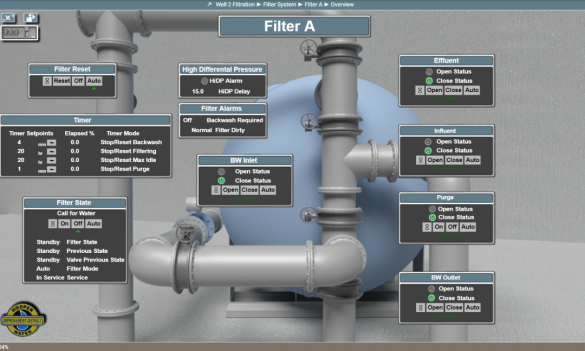
Dorsett Controls InfoScan
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to expose sensitive information, resulting in data theft and misuse of credentials. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following Dorsett Controls products are affected: 3.2 Vulnerability Overview 3.2.1 EXPOSURE OF…
AVTECH IP Camera
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to inject and execute commands as the owner of the running process. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following AVTECH IP camera was identified as being affected; it is…
Johnson Controls exacqVision Client and exacqVision Server
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to be able to decrypt communications between exacqVision Server and exacqVision Client due to insufficient key length and exchange. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Johnson Controls reports that the…
Cisco Smart Software Manager On-Prem Password Change Vulnerability
Summary A vulnerability in the authentication system of Cisco Smart Software Manager On-Prem (SSM On-Prem) could allow an unauthenticated, remote attacker to change the password of any user, including administrative users. This vulnerability is due to improper implementation of the password-change process. An attacker could…
Cisco Secure Email Gateway Arbitrary File Write Vulnerability
Summary A vulnerability in the content scanning and message filtering features of Cisco Secure Email Gateway could allow an unauthenticated, remote attacker to overwrite arbitrary files on the underlying operating system. This vulnerability is due to improper handling of email attachments when file analysis and…
Siemens RUGGEDCOM APE 1808
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow remote attackers to bypass integrity checks. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following products of Siemens are affected: 3.2 Vulnerability Overview 3.2.1 TRUNCATION OF SECURITY-RELEVANT INFORMATION CWE-222 The SSH transport protocol with…
Siemens SIMATIC WinCC
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an unauthenticated remote attacker to retrieve information such as users and passwords. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Siemens reports that the following versions of SIMATIC WinCC are affected: 3.2 Vulnerability Overview…
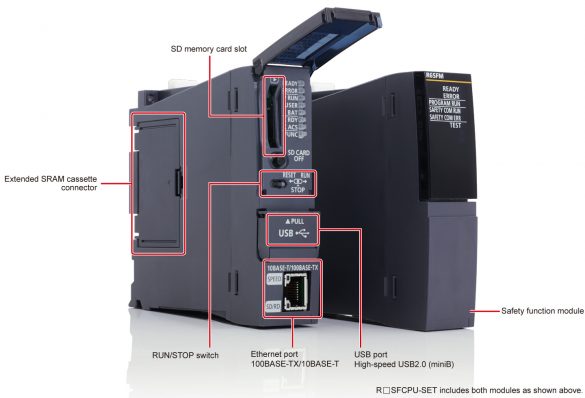
Mitsubishi Electric MELSEC iQ-R, iQ-L Series and MELIPC Series (Update D)
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of this vulnerability could allow a remote attacker to cause a denial-of-service condition in the module’s ethernet communication. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Mitsubishi Electric reports this vulnerability affects the following MELSEC iQ-R, iQ-L series CPU…
Siemens SCALANCE XM-400, XR-500
1. EXECUTIVE SUMMARY 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to cause a memory leak or execute arbitrary code. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following Siemens products, are affected: 3.2 Vulnerability Overview 3.2.1 INADEQUATE ENCRYPTION STRENGTH CWE-326 AES OCB…








Stay connected