BD Alaris PCU (Update A)
1. EXECUTIVE SUMMARY CVSS v3 5.3 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Becton, Dickinson and Company (BD) Equipment: Alaris PCU Vulnerability: Uncontrolled Resource Consumption 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-20-170-06 BD Alaris PCU that was published June 18,…
Johnson Controls exacqVision (Update A)
1. EXECUTIVE SUMMARY CVSS v3 6.8 ATTENTION: Exploitable remotely Vendor: Exacq Technologies, a subsidiary of Johnson Controls Equipment: exacqVision Vulnerability: Improper Verification of Cryptographic Signature 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker with administrative privileges to potentially download and run a malicious executable that…
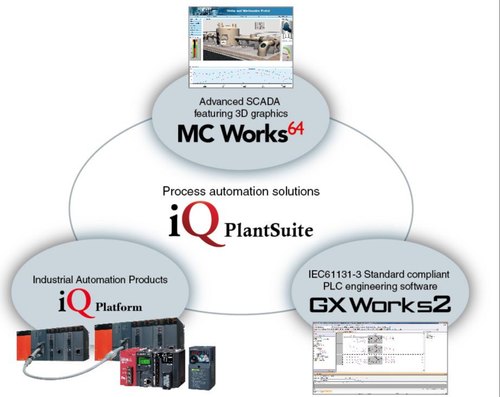
Mitsubishi Electric MC Works64, MC Works32
1. EXECUTIVE SUMMARY CVSS v3 9.4 ATTENTION: Exploitable remotely Vendor: Mitsubishi Electric Equipment: MC Works64, MC Works32 Vulnerabilities: Out-of-bounds Write, Deserialization of Untrusted Data, Code Injection 2. RISK EVALUATION Successful exploitation of these vulnerabilities may allow remote code execution, a denial-of-service condition, information disclosure, or information tampering. 3. TECHNICAL…
ICONICS GENESIS64, GENESIS32
1. EXECUTIVE SUMMARY CVSS v3 9.4 ATTENTION: Exploitable remotely Vendor: ICONICS Equipment: GENESIS64, GENESIS32 Vulnerabilities: Out-of-Bounds Write, Deserialization of Untrusted Data, Code Injection 2. RISK EVALUATION Successful exploitation of these vulnerabilities may allow remote code execution or denial of service. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following products…
Rockwell Automation FactoryTalk Services Platform
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level. Vendor: Rockwell Automation Equipment: FactoryTalk Services Platform Vulnerability: Improper Input Validation 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an unauthenticated attacker to execute remote COM objects with elevated privileges. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS…
Rockwell Automation FactoryTalk View SE
1. EXECUTIVE SUMMARY CVSS v3 9.0 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Rockwell Automation Equipment: FactoryTalk View SE Vulnerabilities: Improper Input Validation, Improper Restriction of Operations Within The Bounds of a Memory Buffer, Permissions, Privileges, and Access Controls, Exposure of Sensitive Information to an Unauthorized Actor 2….
Treck TCP/IP Stack (Update B)
1. EXECUTIVE SUMMARY CVSS v3 10.0 ATTENTION: Exploitable remotely Vendor: Treck Inc. Equipment: TCP/IP Vulnerabilities: Improper Handling of Length Parameter Inconsistency, Improper Input Validation, Double Free, Out-of-bounds Read, Integer Overflow or Wraparound, Improper Null Termination, Improper Access Control CISA is aware of a public report, known as “Ripple20” that…
Treck TCP/IP Stack (Update A)
1. EXECUTIVE SUMMARY CVSS v3 10.0 ATTENTION: Exploitable remotely Vendor: Treck Inc. Equipment: TCP/IP Vulnerabilities: Improper Handling of Length Parameter Inconsistency, Improper Input Validation, Double Free, Out-of-bounds Read, Integer Overflow or Wraparound, Improper Null Termination, Improper Access Control CISA is aware of a public report, known as “Ripple20” that…
Mitsubishi Electric MELSEC iQ-R series (Update A)
1. EXECUTIVE SUMMARY CVSS v3 5.3 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Mitsubishi Electric Equipment: MELSEC iQ-R series Vulnerability: Resource Exhaustion 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled “ICSA-20-161-02 Mitsubishi Electric MELSEC iQ-R series” that was published June 9, 2020…
Philips IntelliBridge Enterprise IBE
1. EXECUTIVE SUMMARY CVSS v3 2.0 Vendor: Philips Equipment: IntelliBridge Enterprise (IBE) Vulnerability: Insertion of Sensitive Information into Log File 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to access credentials to the hospital’s clinical information systems (EMR). 3. TECHNICAL DETAILS…







Stay connected