Legal Notice
All information products included in http://ics-cert.us-cert.gov are provided “as is” for informational purposes only. The Department of Homeland Security (DHS) does not provide any warranties of any kind regarding any information contained within. DHS does not endorse any commercial product or service, referenced in this product or otherwise. Further dissemination of this product is governed by the Traffic Light Protocol (TLP) marking in the header.
1. EXECUTIVE SUMMARY
-
CVSS v3 8.6
- ATTENTION: Remotely exploitable/Low skill level to exploit
- Vendor: Yokogawa
- Equipment: iDefine, STARDOM, ASTPLANNER, and TriFellows
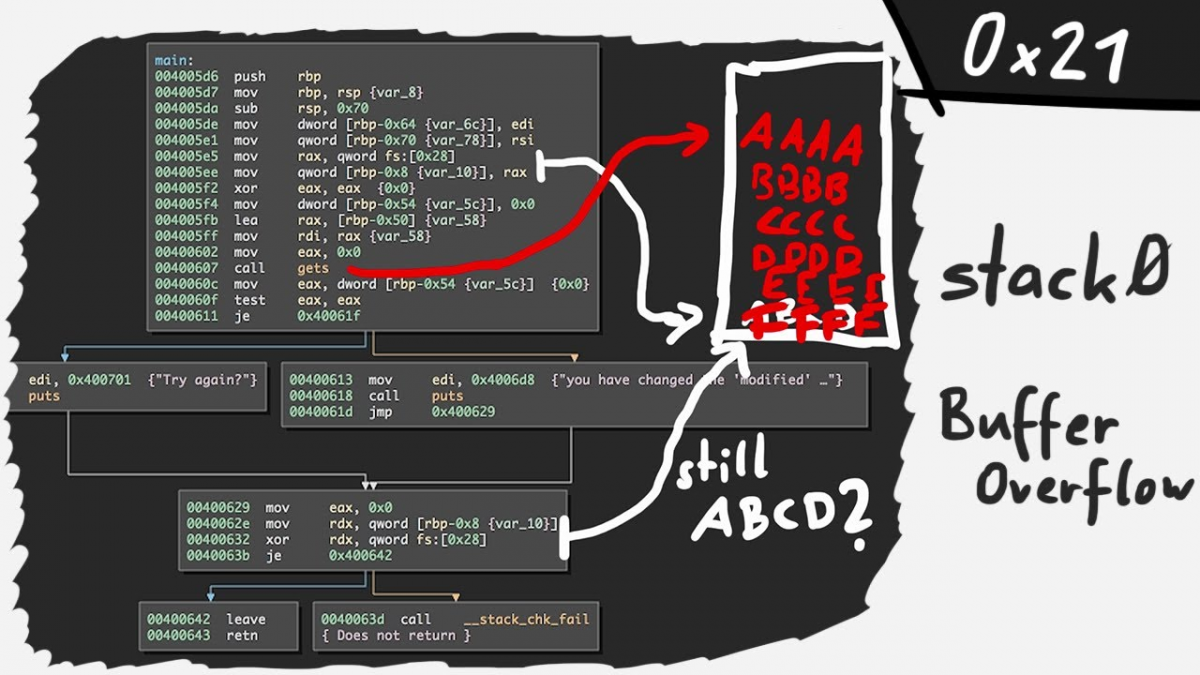
- Vulnerability: Stack-based Buffer Overflow
2. RISK EVALUATION
Successful exploitation of this vulnerability may allow arbitrary code execution, or the stopping of the license management function.
3. TECHNICAL DETAILS
3.1 AFFECTED PRODUCTS
According to Yokogawa the following products are affected:
- ASTPLANNER: R15.01 and prior,
- iDefine for ProSafe-RS: R1.16.3 and prior,
- STARDOM: VDS R7.50 and prior and FCN/FCJ Simulator R4.20 and prior, and
- TriFellows: Version 5.04 and prior.
3.2 VULNERABILITY OVERVIEW
3.2.1 STACK-BASED BUFFER OVERFLOW CWE-121
This vulnerability that affects the license management function when it receives specially crafted data. An attacker could overflow the buffer by exploiting this, which may result in the license management function stopping or result in arbitrary code execution.
CVE-2018-0651 has been assigned to this vulnerability. A CVSS v3 base score of 8.6 has been calculated; the CVSS vector string is (AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:H).
3.3 BACKGROUND
- CRITICAL INFRASTRUCTURE SECTORS: Critical Manufacturing, Energy, and Food and Agriculture
- COUNTRIES/AREAS DEPLOYED: Worldwide
- COMPANY HEADQUARTERS LOCATION: Japan
3.4 RESEARCHER
Yokogawa worked with JPCERT to report this vulnerability to NCCIC.
4. MITIGATIONS
Yokogawa recommends users to update to the latest versions or apply the patch:
ASTPLANNER: Update to R15.02.01 or contact support for the patch,
- iDefine for ProSafe-RS: Update to R1.16.4,
- STARDOM: Update to VDS R8.10 or contact support for the patch, and
- TriFellows: Update to Version 5.10 or contact support for the patch.
- Support:
- iDefine for ProSafe-RS and STARDOM users: https://contact.yokogawa.com/cs/gw?c-id=000498
- ASTPLANNER and TriFellows users: https://contact.yokogawa.com/cs/gw?c-id=000497
When Yokogawa service personnel perform system upgrade or install patches, those charges are borne by the user. Please contact support in the following section for the countermeasures regarding the affected products. Yokogawa strongly suggests all users to introduce appropriate security measures not only for the vulnerability identified, but also to the overall systems.
Refer to Yokogawa’s security notification YSAR-18-0006 for more information, which can be located here:
https://www.yokogawa.com/library/resources/white-papers/yokogawa-security-advisory-report-list/
NCCIC recommends users take defensive measures to minimize the risk of exploitation of this vulnerability. Specifically, users should:
- Minimize network exposure for all control system devices and/or systems, and ensure that they are not accessible from the Internet.
- Locate control system networks and remote devices behind firewalls, and isolate them from the business network.
- When remote access is required, use secure methods, such as Virtual Private Networks (VPNs), recognizing that VPNs may have vulnerabilities and should be updated to the most current version available. Also recognize that VPN is only as secure as the connected devices.
NCCIC reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures.
Source:
https://ics-cert.us-cert.gov/advisories/ICSA-18-233-01

Stay connected