Siemens SiNVR 3
1. EXECUTIVE SUMMARY CVSS v3 8.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SiNVR 3 Vulnerabilities: Path Traversal, Cleartext Storage in a File or on Disk, SQL Injection, Cross-site Scripting, Insufficient Logging Improper Input Validation, Weak Cryptography for Passwords 2. RISK EVALUATION Successful exploitation of these…
SIMATIC S7-300 CPUs and SINUMERIK Controller over Profinet
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC S7-300 CPUs and SINUMERIK Controller over Profinet Vulnerability: Uncontrolled Resource Consumption 2. RISK EVALUATION Successful exploitation of this vulnerability could cause the affected device to go into defect mode resulting in a…
Siemens Spectrum Power 5
1. EXECUTIVE SUMMARY CVSS v3 6.1 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Spectrum Power 5 Vulnerability: Improper Neutralization of Script-Related HTML Tags in a Web Page (Basic XSS) 2. RISK EVALUATION Successful exploitation of this vulnerability could affect the confidentiality or integrity of the data…
Johnson Controls Kantech EntraPass
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Kantech, a subsidiary of Johnson Controls Equipment: EntraPass Vulnerability: Improper Input Validation 2. RISK EVALUATION Successful exploitation of this vulnerability could allow malicious code execution with system-level privileges. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The…
Johnson Controls Metasys
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Johnson Controls Equipment: Metasys Vulnerability: Improper Restriction of XML External Entity Reference 2. RISK EVALUATION Successful exploitation of this vulnerability can allow a denial-of-service attack or disclosure of sensitive data. 3. TECHNICAL DETAILS 3.1 AFFECTED…
Rockwell Automation MicroLogix Controllers and RSLogix 500 Software
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Rockwell Automation Equipment: MicroLogix 1400 Controllers, MicroLogix 1100 Controllers, and RSLogix 500 Software Vulnerabilities: Use of Hard-coded Cryptographic Key, Use of a Broken or Risky Algorithm for Password Protection, Use of Client-Side Authentication, Cleartext Storage…
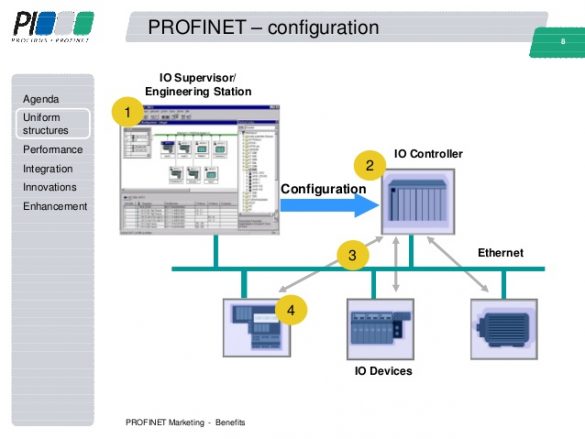
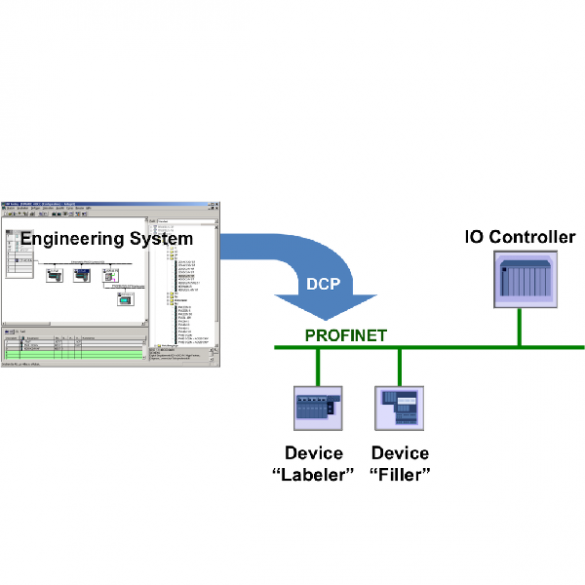
Siemens PROFINET-IO Stack (Update A)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: Siemens PROFINET-IO Stack Vulnerability: Uncontrolled Resource Consumption 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-20-042-04 Siemens PROFINET-IO Stack that was published February 11, 2020, to the…
Siemens SIMATIC S7 (Update A)
1. EXECUTIVE SUMMARY CVSS v3 5.3 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC S7 Vulnerability: Uncontrolled Resource Consumption (Resource Exhaustion) 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-20-042-05 Siemens SIMATIC S7 that was published February 11, 2020, on…
Siemens SIMATIC PCS 7, SIMATIC WinCC, and SIMATIC NET PC (Update A)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low skill level to exploit Vendor: Siemens Equipment: SIMATIC PCS 7, SIMATIC WinCC, SIMATIC NET PC Vulnerability: Incorrect Calculation of Buffer Size 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-19-042-06 ICSA-20-042-06 Siemens SIMATIC PCS…
Siemens SIMATIC S7-1500 (Update A)
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely Vendor: Siemens Equipment: SIMATIC S7-1500 CPU family Vulnerability: Resource Exhaustion 2. UPDATE INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-20-042-11 Siemens SIMATIC S7-1500 that was published February 11, 2020, to the ICS webpage on us-cert.gov….








Stay connected