Hitachi Energy AFF660/665 Series
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low attack complexity Vendor: Hitachi Energy Equipment: AFF660/665 Firewall Vulnerability: Stack-based Buffer Overflow 2. RISK EVALUATION Successful exploitation of this vulnerability could overflow a buffer on the device and fully compromise it. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following versions…
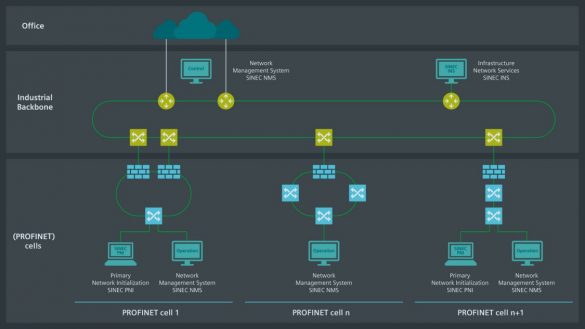
Siemens SINEC INS
1. EXECUTIVE SUMMARY CVSS v3 8.8 ATTENTION: Exploitable remotely/Low attack complexity Vendor: Siemens Equipment: SINEC INS Vulnerabilities: Improper Input Validation, Integer Overflow or Wraparound, Uncontrolled Resource Consumption, Command Injection, Inadequate Encryption Strength, Missing Encryption of Sensitive Data, Improper Restriction of Operations Within the Bounds of a Memory Buffer, Exposure…
Delta Industrial Automation DIAEnergie
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/Low attack complexity Vendor: Delta Industrial Automation Equipment: DIAEnergie Vulnerability: Use of Hard-coded Credentials 2. RISK EVALUATION Successful exploitation of this vulnerability could lead to remote code execution. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Delta Industrial Automation reports the following versions…
AVEVA Edge 2020 R2 SP1 and all prior versions
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low attack complexity Vendor: AVEVA Equipment: AVEVA Edge 2020 R2 SP1 and all prior versions Vulnerabilities: Insufficient UI Warning of Dangerous Operations, Uncontrolled Search Path Element, Deserialization of Untrusted Data, Improper Restriction of XML External Entity Reference 2. RISK EVALUATION Successful exploitation…
Hitachi Energy TXpert Hub CoreTec 4
1. EXECUTIVE SUMMARY CVSS v3 6.0 Vendor: Hitachi Energy Equipment: TXpert Hub CoreTec 4 Vulnerabilities: Authentication Bypass Using an Alternate Path or Channel, Improper Input Validation, Download of Code Without Integrity Check 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to cause a denial-of-service…
Delta Electronics DOPSoft 2 (Update A)
1. EXECUTIVE SUMMARY CVSS v3 7.8 ATTENTION: Low attack complexity Vendor: Delta Electronics Equipment: DOPSoft 2 Vulnerabilities: Stack-based Buffer Overflow, Out-of-Bounds Write, Heap-based Buffer Overflow 2. UPDATED INFORMATION This updated advisory is a follow-up to the original advisory titled ICSA-21-252-02 Delta Electronics DOPSoft 2 that was published September 9,…
Mitsubishi Electric Multiple Factory Automation Products (Update B)
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low attack complexity Vendor: Mitsubishi Electric Equipment: GOT2000 compatible HMI software, CC-Link IE TSN Industrial Managed Switch, MELSEC iQ-R Series OPC UA Server Module Vulnerabilities: Infinite Loop, OS Command Injection 2. UPDATE INFORMATION This updated advisory is a follow-up to the…
Hitachi Energy MSM Product
1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low attack complexity Vendor: Hitachi Energy Equipment: MSM Product Vulnerability: Reliance on Uncontrolled Component 2. RISK EVALUATION Successful exploitation of this vulnerability could disrupt the functionality of the MSM web interface, steal sensitive user credentials, or cause a denial-of-service condition. 3….
Siemens Linux-based Products (Update J)
1. EXECUTIVE SUMMARY 2. UPDATE INFORMATION This updated advisory is a follow-up to the advisory update titled ICSA-21-131-03 Siemens Linux-based Products (Update I) that was published August 11, 2022, to the ICS webpage at www.cisa.gov/ics. 3. RISK EVALUATION Successful exploitation of this vulnerability could compromise…
Schneider Electric EcoStruxure, EcoStruxure Process Expert, SCADAPack RemoteConnect for x70
1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low attack complexity Vendor: Schneider Electric Equipment: EcoStruxure, EcoStruxure Process Expert, SCADAPack RemoteConnect for x70 Vulnerabilities: Heap-based Buffer Overflow, Wrap or Wraparound, Classic Buffer Overflow, Out-of-bounds Write 2. RISK EVALUATION The successful exploitation of these vulnerabilities on the affected products could…









Stay connected